Top 9 NGFW Solutions for 2023

Next-generation firewalls (NGFW) are the wave of the future for small businesses to large enterprises. So far, in 2023, they represent a 20% market share! These advanced firewalls improve the existing technology, enabling more security features than traditional ones.
Generally, firewalls can only grow as challenges advance. So security teams must rise to meet them with better protection. That’s where NGFWs come into play. They’re more effective than your traditional firewalls and are great for SMBs that don’t have a large dedicated security team. So let’s dig into why they’re great for SMBs and some of our top NGFWs.
Why Are Next-Generation Firewalls Important for Small Businesses?
Next-generation firewalls offer more than just port/protocol info and inspection. Newer protocols and rules provide robust security for constant monitoring and automatic threat detection and notification. This is important for SMBs, where most employees wear multiple hats. So besides network segmentation and multiple firewalls, you can have one firewall rule them all!
9 NGFW Features to Look For
When buying next-generation firewalls, keep an eye out for essential features traditional firewalls don’t offer. Check out these 9 features and keep them in mind when shopping.
1. Application and Identity Awareness
As mentioned before, it’s not just about analyzing ports and protocols. Next-generation firewalls also have new abilities to recognize identities that help administrators to enable access protocols. This access can be based on specific criteria. As a result, you’re able to give the right access to the right people without worrying about anyone breaking the rules.
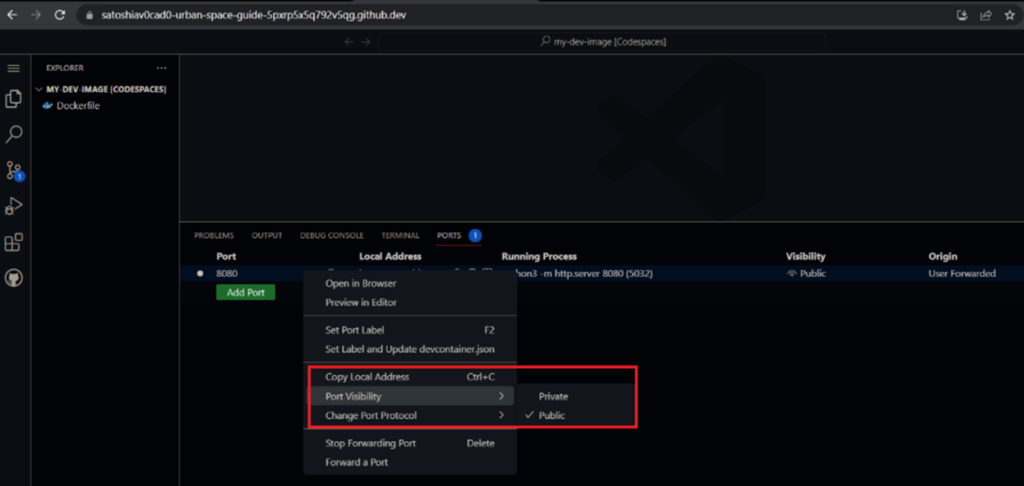
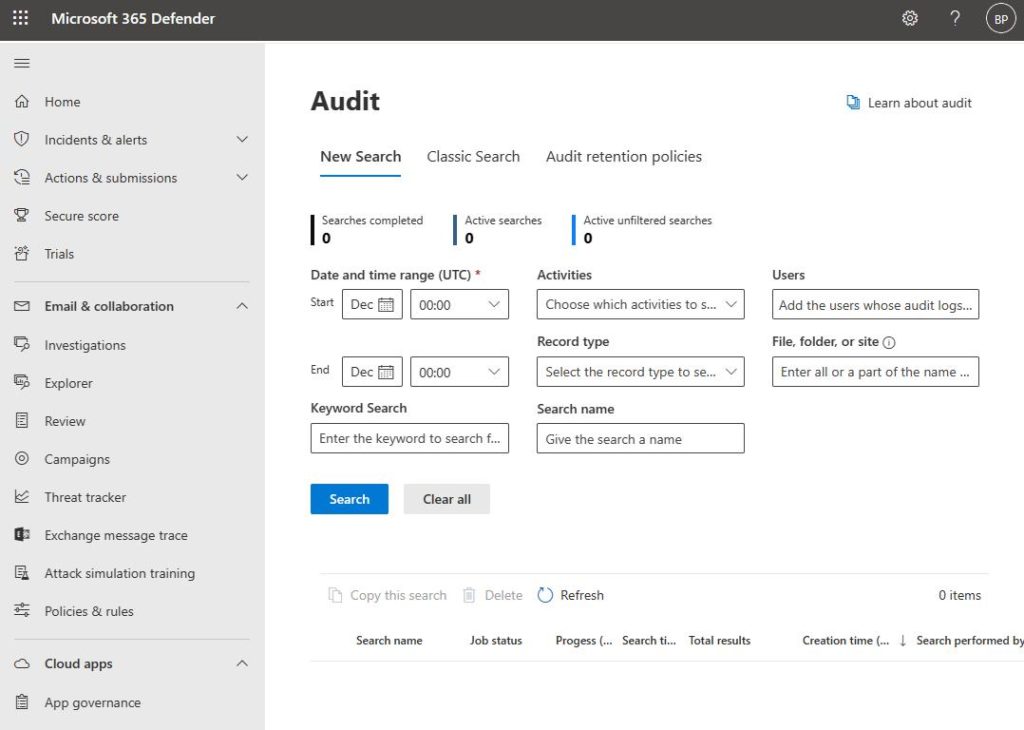
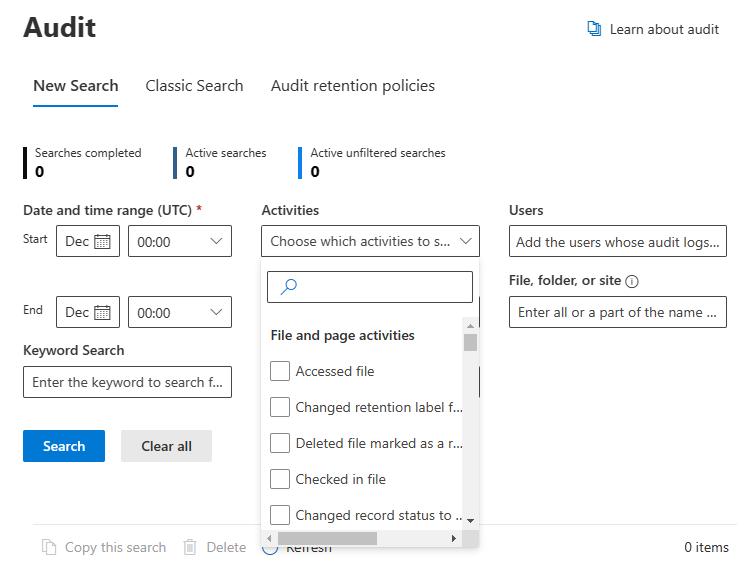
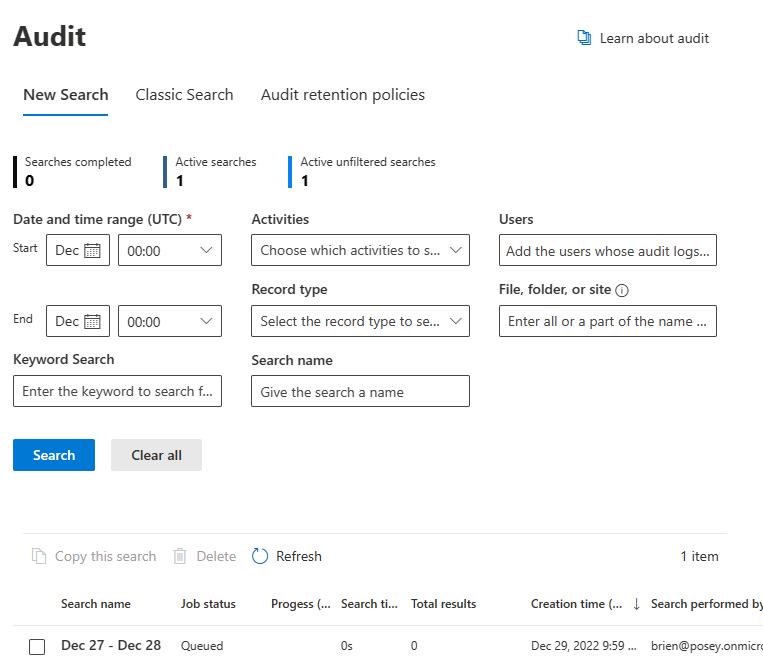
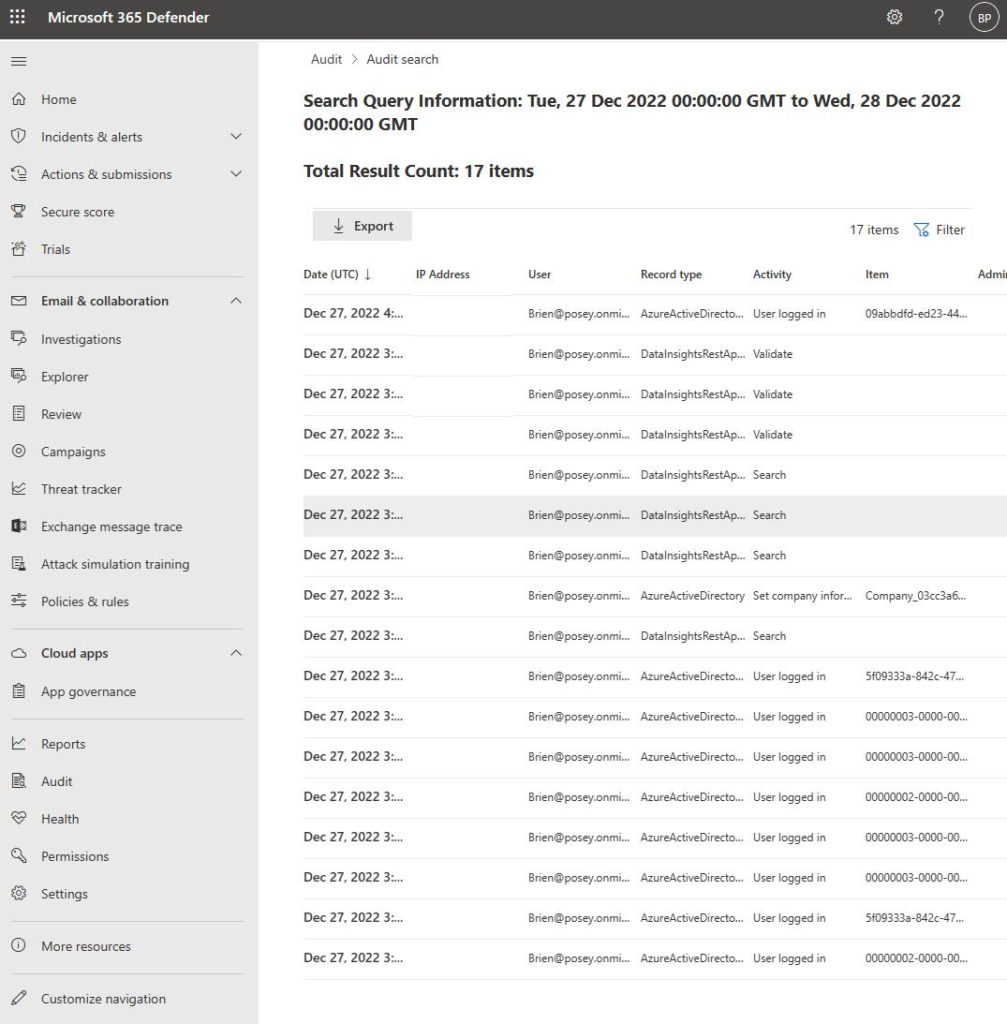
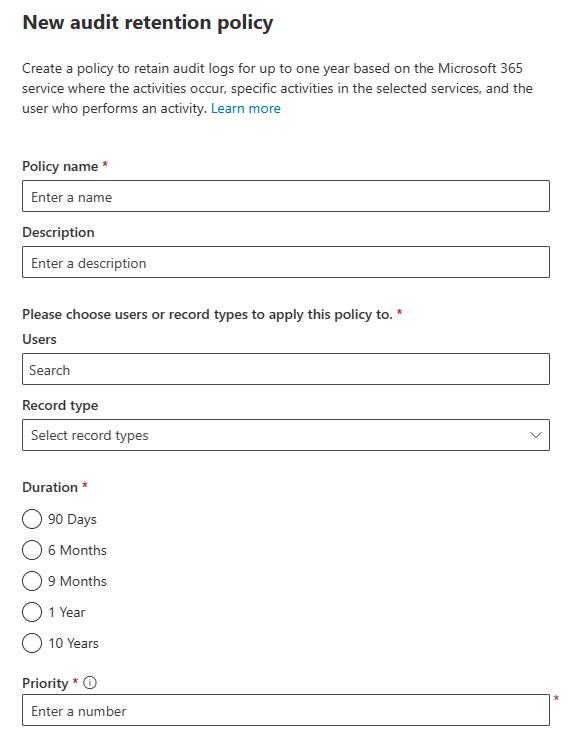
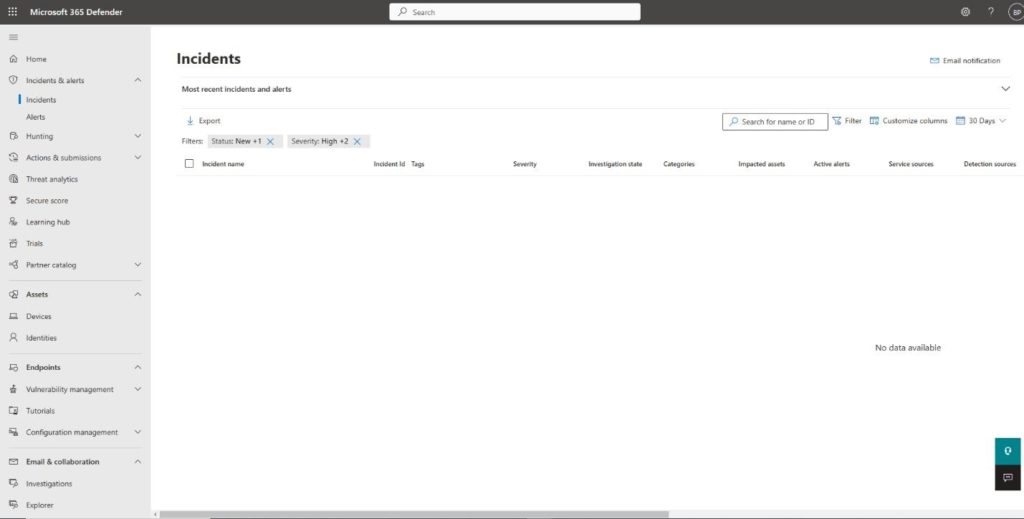
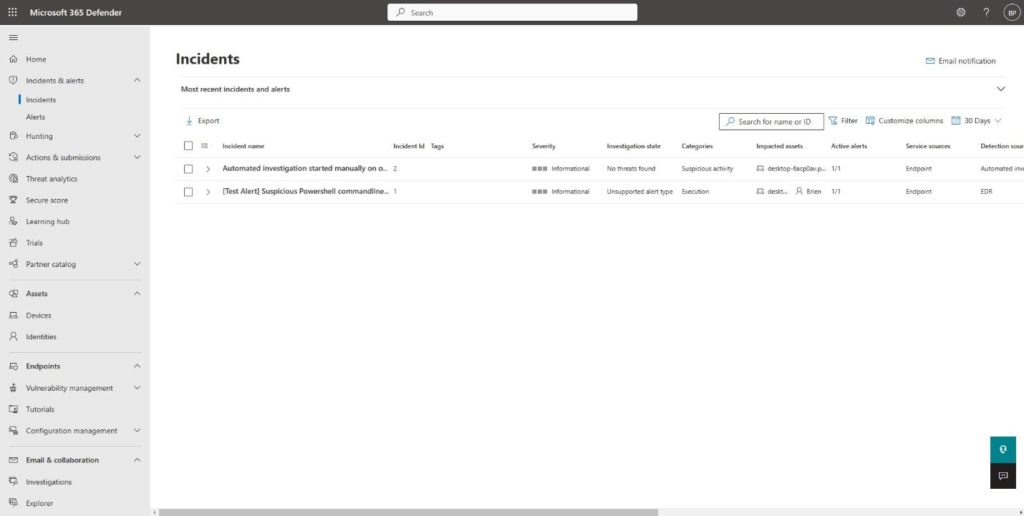
2. Centralized Management, Visibility, and Auditing
Administrators need access to a user-friendly interface to view and adjust various security systems, like NGFW devices. NGFWs typically include features like log analysis, policy management, and a management dashboard. These features allow admins to monitor the network’s overall status, examine traffic patterns, and export firewall configurations.
3. Stateful Inspection
Traditional firewalls generally inspect network traffic up to Layer 4 using stateful inspection. In contrast, NGFWs inspect traffic at Layers 2-7, providing a more comprehensive view of network traffic. This improvement allows NGFWs to perform the same packet-inspecting duties as traditional firewalls while also being able to identify safe and unsafe packets. Extending this to the application layer is extremely valuable as more and more important resources are located at the network edge.
4. Deep Packet Inspection (DPI)
DPI takes packet inspection one step further by inspecting the content of the packets rather than just the headers. It performs this inspection by looking into both the data and header parts of the transmitted packets. DPI can identify, classify, prevent, or redirect packets that contain suspicious code or payloads that stateful inspection might miss.
5. Integrated Intrusion Prevention (IPS)
As cybersecurity technology has evolved, IPS has become an increasingly popular feature in next-generation firewalls. While the differences between these two types of products are becoming less distinct, this creates a challenge for buyers. They have to decide whether the IPS technology included in their NGFW is good enough compared to a standalone product. IPS plays a crucial role in preventing attacks like brute force, known vulnerabilities, and DoS attacks.
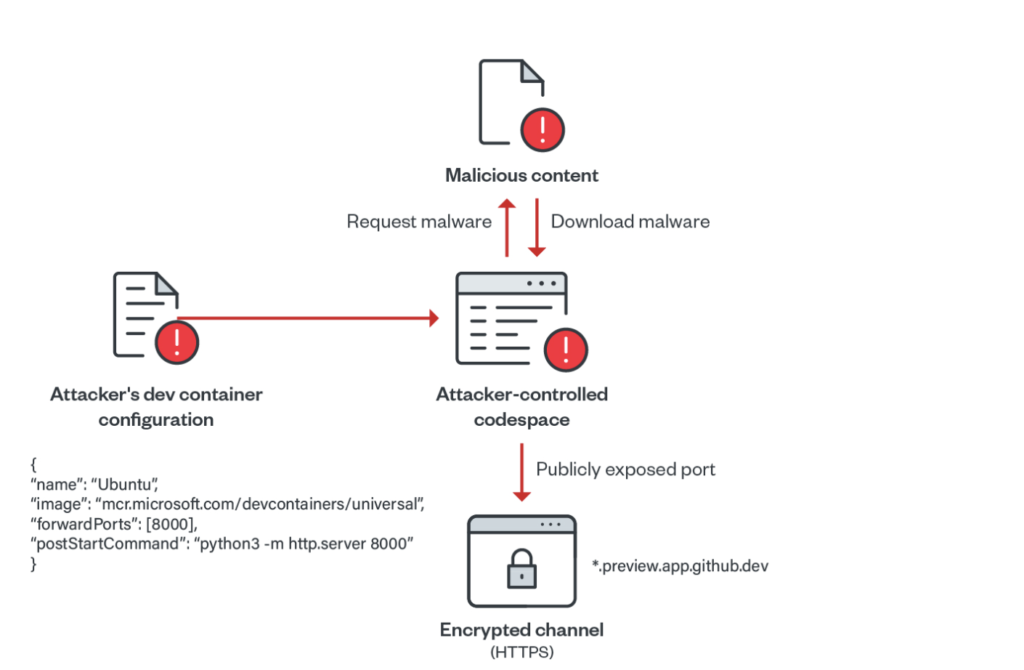
6. Network Sandboxing
Depending on your NGFW, you may be able to use network sandboxing, a method of advanced malware protection. It allows IT professionals to send potentially malicious programs to a safe, isolated, cloud-based environment to analyze for security purposes.
7. Secured Traffic
HTTPS is currently the norm for secure communication over the internet, utilizing the SSL/TLS protocol to encrypt traffic. As next-generation firewalls have become the leading network traffic inspection device, they have been adapted to decrypt SSL and TLS communications, frequently including features like remote access VPN. This type of monitoring ensures the infrastructure can detect and prevent any potential threats that may be under wraps.
8. Threat Intelligence and Dynamic Lists
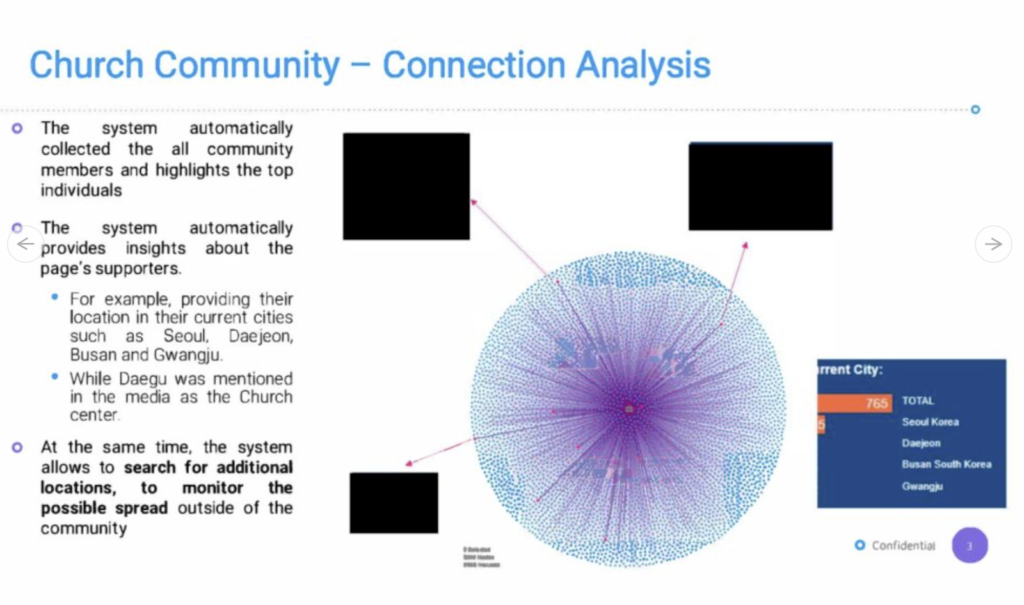
Generally, next-generation firewalls offer some type of threat intelligence feature. As new cyber threats appear regularly, it’s unrealistic to expect admins to monitor and respond constantly. NGFWs can use threat intelligence feeds from external sources to stay updated on the latest threats and attack origins. They use this information to block or automatically eliminate malicious traffic or flag events requiring attention. With threat intelligence feeds and dynamic lists at their disposal, NGFWs make threat hunting more automated and less prone to human error.
9. Integration Capacity
Regardless of their size, many businesses increasingly use third-party services to improve their operations and processes. This includes a wide range of popular and essential SaaS applications and APIs. As IT managers evaluate new products to incorporate into their organization’s infrastructure, these products must have the ability to integrate easily with third-party applications. For example, integrations include SIEM software, 2FA, Active Directory, and reporting tools.
Without further ado, let’s dive into the top NGFWs on the market for 2023.
Top 9 Next-Generation Firewalls for 2023

Source: Pixybay
After a thorough review of different key security aspects, we’ve arrived at our top picks for 2023!
1. Palo Alto Networks
Palo Alto Networks has a comprehensive set of next-generation firewalls. These include physical appliances, virtualized firewalls, and container firewalls. The firewalls are based on a consistent single-pass architecture and can inspect all types of traffic, including applications, threats, and content.
In particular, they can link the traffic to a specific user, regardless of their location or device type. Their NGFWs can also secure businesses that use multiple clouds with their cloud identity engine and protect from the increasing use of SaaS applications with an integrated Cloud Access Security Broker.
2. Fortinet
Fortinet offers a wide range of firewall products, suitable for different deployment use cases and available on public cloud platforms. They also continually develop their firewall services, providing customers with access to cutting-edge security tools necessary.
Their next-generation firewalls also come with high-performance appliances, adding intrusion prevention, application control, and anti-malware to traditional firewall-VPN combinations. So Fortinet gives you one platform for end-to-end security across your network.
3. Check Point
Check Point offers a wide range of features and capabilities, including stateful inspection, VPN support, and intrusion prevention. It also features a SmartConsole management console that allows admins to easily configure and manage firewall policies and view real-time security events and statistics. Check Point is well-known for being the solution of choice for several large enterprises and government organizations.
4. Barracuda
Barracuda is a hardware-based firewall designed to provide comprehensive security for small and medium-sized businesses. One of the main advantages of the Barracuda firewall is its ease of management with a web interface that makes it easy for admins to set up and maintain firewalls.
Additionally, Barracuda provides a cloud-based management and reporting platform to help admins manage multiple firewalls from a single console. Their firewall is a good option for SMBs as it’s relatively affordable and has a good balance of features and accessibility.
5. Cisco
Cisco offers a variety of firewall options that can scale from small branch offices to large carrier-grade data centers. These firewalls are also available in virtual form, which allows for security in both private and public cloud environments.
Their Secure Firewall 3100 series is designed for hybrid work environments, providing remote workers with up to 17 times faster VPN performance. These firewalls use machine learning to passively identify user applications and potential threats in encrypted traffic without decrypting.
6. Forcepoint
Forcepoint offers a variety of network security solutions, including 9 different firewall series designed for different purposes. They include central management and extensive security features like VPN, IPS, encrypted inspection, SD-WAN, and more.
Their NGFW intends to simplify getting a network running securely and efficiently and keep it that way. The Forcepoint NGFW is built around a unified software core that provides consistent capabilities, acceleration, and central management across all types of deployments.
7. Juniper
The on-premises devices provided by Juniper can collect and analyze data from any external firewall or data source. This allows companies to quickly respond to threats, detect malware and avoid being tied down to a single vendor.
The Juniper ATP platform functions as an open ecosystem and can be used with any firewall and SIEM system. This makes it highly compatible and able to be implemented quickly in any environment. The platform’s ability to detect and analyze threats, as well as automate response actions, allows for one-touch mitigation of malware. It offers a unique approach to addressing advanced malware.
8. Sophos
Sophos offers next-generation firewall (NGFW) features that allow you to safeguard your network with an enterprise-class firewall while ensuring the safety of your web traffic. It protects against threats like drive-by downloads and botnets and enables secure communication by providing flexible VPN options. Additionally, it offers detailed reports to help you understand and analyze the network’s performance and protection and gives the insight to improve them.
9. KerioControl
KerioControl is a software-based firewall that offers many features, including stateful inspection, VPN support, and intrusion prevention. It also includes content filtering, bandwidth management, and real-time reporting.
One of the key features of Kerio Control is its flexibility and ease of deployment. You can install it on various hardware, including physical servers, virtual machines, and even on a cloud platform like AWS. Kerio Control also offers a comprehensive and intuitive web-based management interface that makes it easy for admins to set up and manage firewall policies.
Kerio Control is a solid firewall solution that is well-suited for small and medium-sized businesses and provides a good balance of features and accessibility. It can be easily deployed in a variety of scenarios making it a versatile option for different businesses.
Before we wrap up, I’ll quickly take you through some of the top firewall trends in 2023 that you should know about.
Firewall Trends in 2023

Source: Unsplash
In 2023, we can expect that the industry will continue moving towards the cloud, which provides the same level of protection as traditional firewalls but is more cost-effective and easier to manage. Virtualization and software-defined networking will also be more widely adopted, allowing for scalability and flexibility.
Growth Will Be in Demand for NGFWs
The market for next-generation firewalls is expected to grow in the coming years. Factors like the increasing adoption of cloud-based services, the growing use of mobile and IoT devices, and the rising threat of cyberattacks are all driving demand. Additionally, the growing use of virtualization and software-defined networking contributes to the NGFW market’s growth. The growing focus on compliance and regulatory requirements also drives the need for more advanced security solutions, like NGFWs.
Cloud-Built NGFWs
The future of cloud-built next-generation firewalls is expected to be positive. More and more companies are moving their operations to the cloud, so the demand for cloud-based NGFWs is expected to increase. Cloud-built NGFWs offer many benefits over traditional on-premises NGFWs, including ease of deployment, scalability, and flexibility. Additionally, since the firewall runs on the cloud provider’s infrastructure, it can handle higher traffic loads and provide better performance than on-premises NGFWs.
Time for some quick final words as I wrap up this guide.
Final Words
The NGFWs are pretty revolutionary and are poised to be the market leader in the near term. They are also very beneficial for small businesses since they have a lot of automation, which is very helpful to smaller teams. As security threats become more advanced, so do the security tools that keep them at bay. It would only be wise to jump on the NGFW bandwagon to use the best firewall to secure your network.
Want to learn more about NGFWs or have more questions? Read the FAQ and Resources sections below!
FAQ
What are next-generation firewalls?
A next-generation firewall uses advanced features to protect networks from cyber threats, like intrusion prevention, application control, and malware protection. NGFWs provide a higher level of security than traditional firewalls.
What are the benefits of next-generation firewalls?
NGFWs provide a higher level of security than traditional firewalls, including intrusion prevention, application control, and malware protection. Additionally, they offer better visibility into network traffic and allow you to control access to network resources based on user identity.
How do next-generation firewalls differ from traditional firewalls?
NGFWs differ from traditional firewalls because they provide additional security features like intrusion prevention, application control, and malware protection. Additionally, they offer better visibility into network traffic and allow you to control access to network resources based on user identity.
How are next-generation firewalls managed?
NGFWs can be managed in several ways, including through a web-based interface or a command-line interface. Some NGFWs also include support for APIs, which allows them to be integrated with other tools and systems.
What types of threats can next-generation firewalls protect against?
NGFWs can protect against a wide range of cyber threats, including intrusion attempts, malware, and malicious traffic. Additionally, many NGFWs also include features like intrusion prevention, application control, and malware protection, which can help to protect networks from a wide range of threats.
Resources
TechGenix: Article on Stateful and Stateless Firewalls
Learn about the differences between stateful and stateless firewalls and how they can benefit your organization.
TechGenix: Article on VPN and Firewall Security
Explore VPN and firewall security solutions for your business.
TechGenix: Article on 5 Firewall Best Practices
Discover five firewall best practices you should implement in your business.
TechGenix: Article on Firewall as a Service (FWaaS) Vendors
Get acquainted with some of the top FWaaS vendors.
TechGenix: Article on Firewall Vendor Strategies
Learn about the different strategies you can use with multiple firewall vendors.
The post Top 9 NGFW Solutions for 2023 appeared first on TechGenix.