We are pleased to announce the general availability of Modern Admin Control Panel (MACP), as part of the Skype for Business Server 2019 March 2021 Cumulative Update.
This is a continuation to our earlier released versions of MACP. You can read about previous releases, Phase 2 March 2020 here and Phase 1 in July 2019 here.
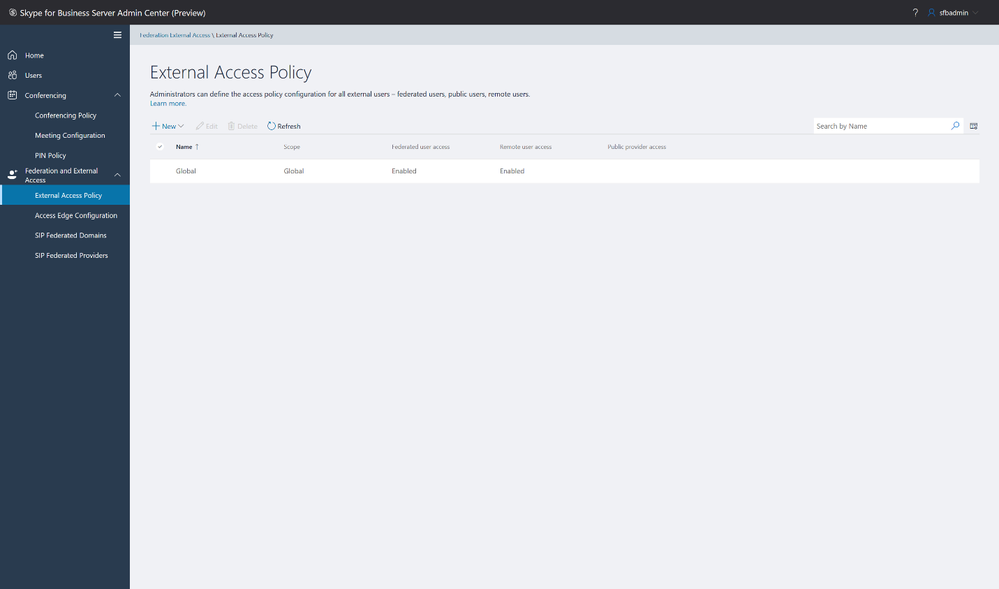
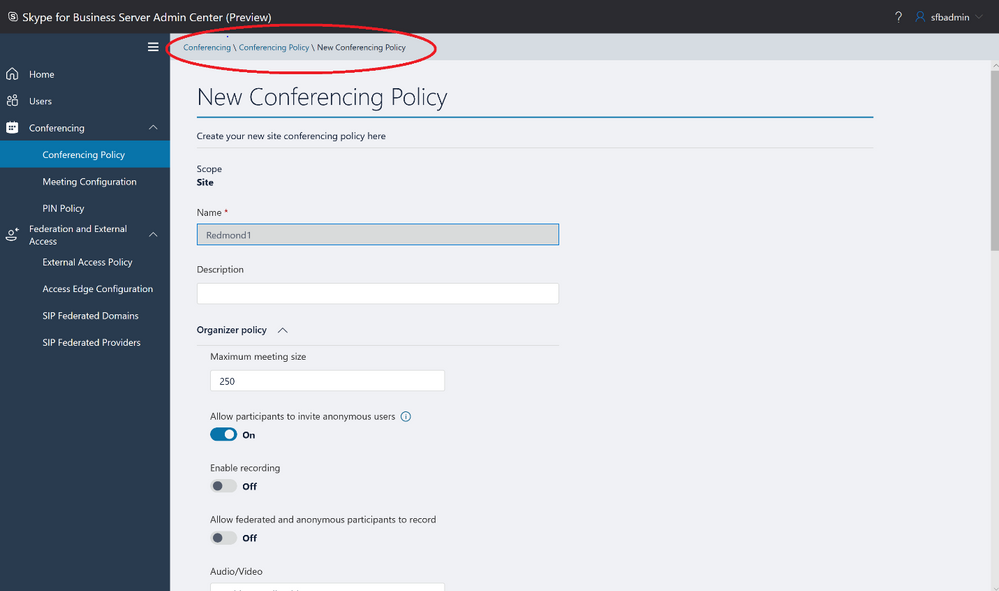
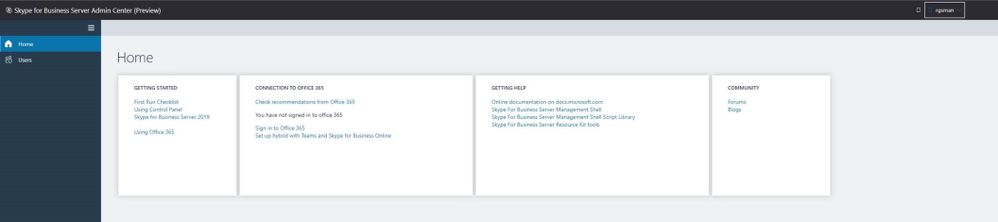
We had covered ‘Home’, ‘Users’, ‘Conferencing’ and ‘Federation and External Access’ tabs in earlier releases. In this release we introduce following tabs: ‘Voice Routing’, ‘Voice Features’, ‘Response Group’ and ‘Conferencing (Dial-In-Access Number sub-tab)’
We continue to listen to our customers to prioritize and ship new features and updates. Hence based on your feedback, this release also includes the following enhancements.
- Addition of OAuth (optional) to login into MACP portal
- Support for Simple URL to access MACP portal
Please start using new Control Panel and share feedback and questions via the ‘Give Feedback’ link in the Control Panel. Read on for details.
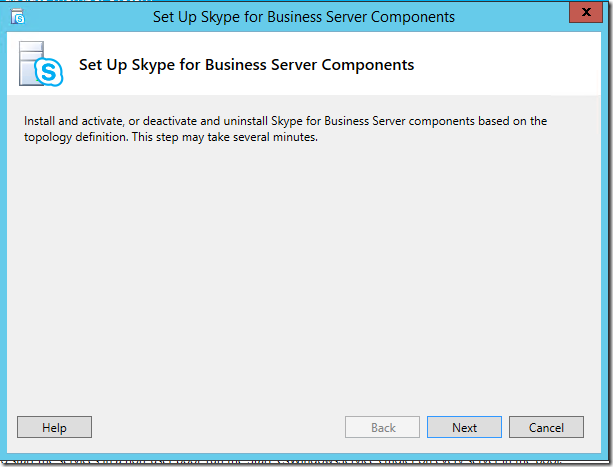
Installation Instructions
1. Run SSUI
2. Run Bootstrapper.exe
3. Please install the Management OData if not installed using below steps:
a. Open PowerShell in Administrator mode
b. Run command: Add-WindowsFeature ManagementOData
The administrator account must have CsAdministrator role privileges and must be SIP enabled. If the OAuth is set up, administrator is not required to be SIP enabled.
Launching and Using Control Panel
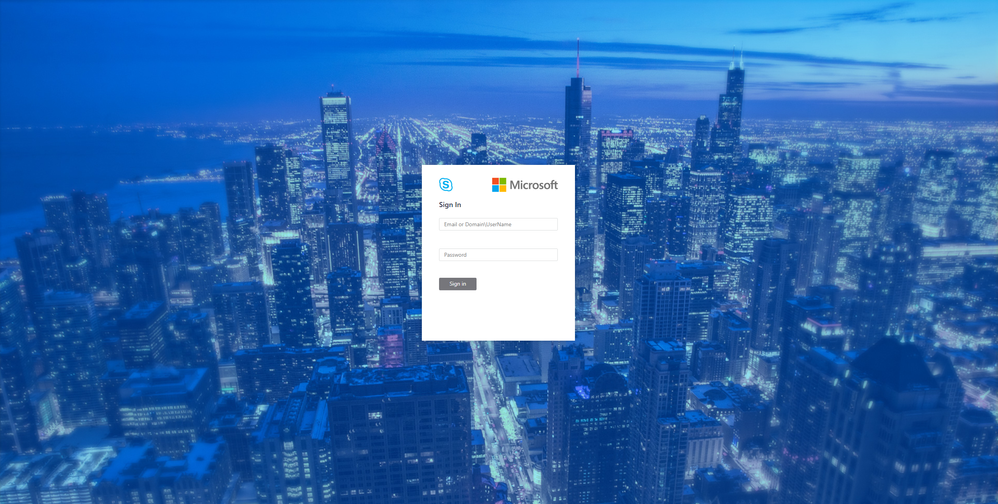
Please put in https://<your pool FQDN>/macp or the configured simple URL https://admin.<your-domain>.com manually in a supported browser, and the Control Panel should open. You can also click on the blue banner at the top of the old Control Panel to launch the new Panel. The login screen looks like the following:
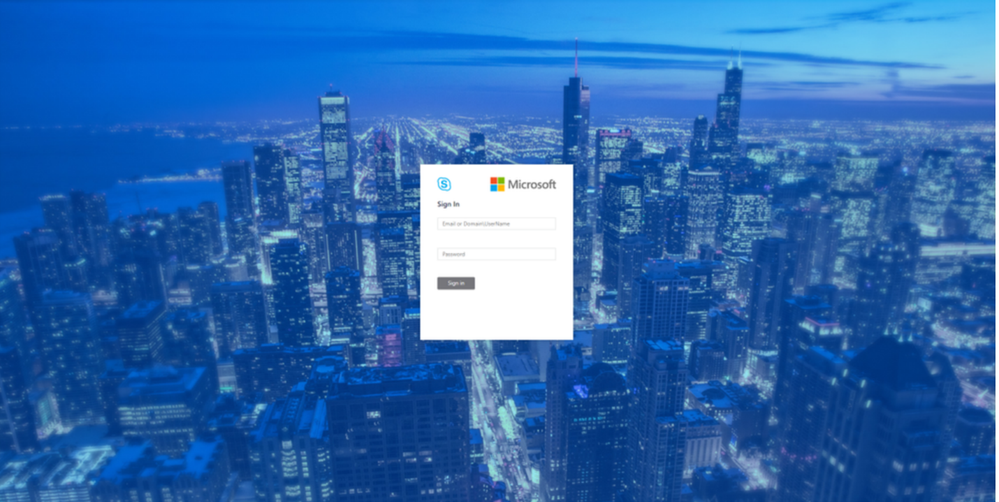 Login screen
Login screen
Once you hit the login screen, log in with your admin credentials.
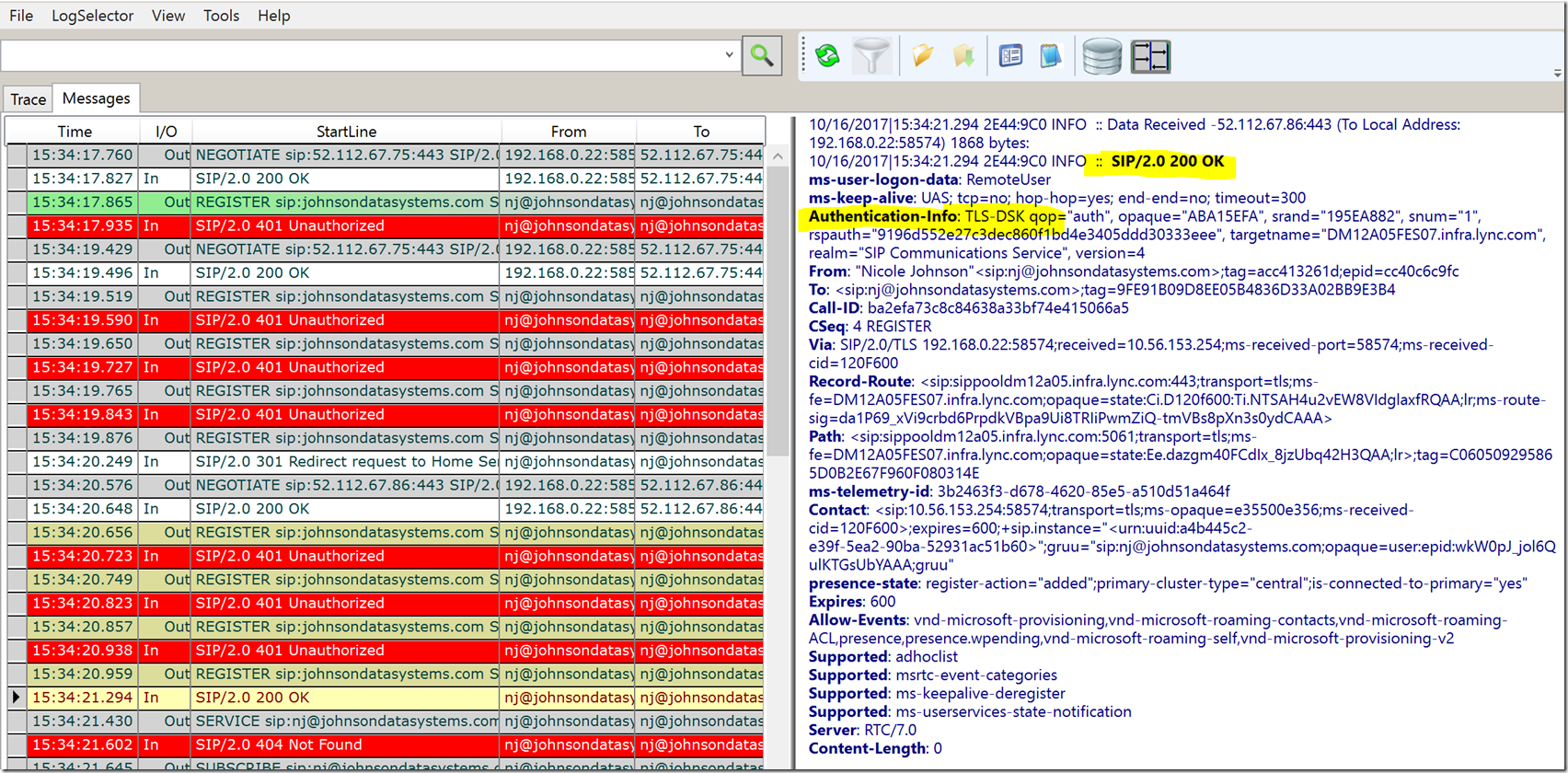
Voice Routing
Please create, modify, or delete dial plans in Dial Plan sub-tab as below:
 Dial Plan Home screen
Dial Plan Home screen
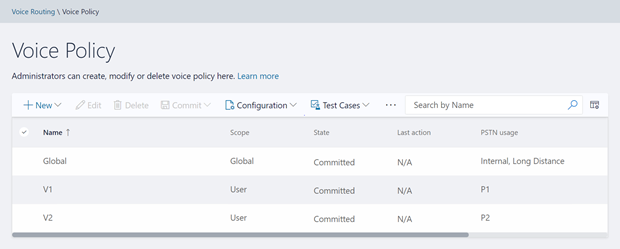
Please create, modify, or delete voice policies in Voice Policy sub-tab as below:
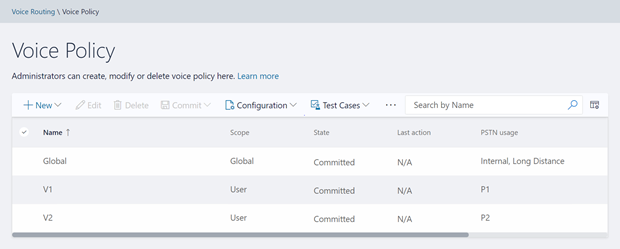 Voice Policy Home screen
Voice Policy Home screen
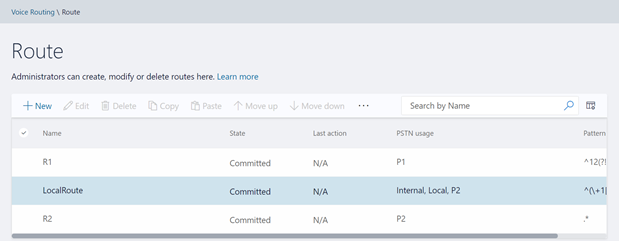
Please create, modify, delete, or change the priority order of routes in the Route sub-tab below:
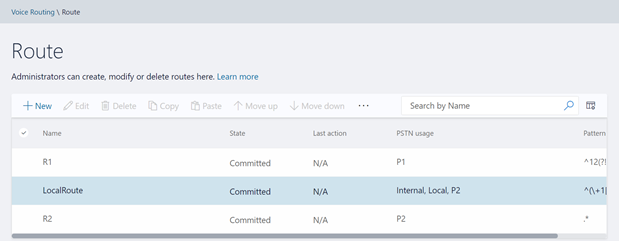 Route Home screen
Route Home screen
Please view or delete PSTN usages in PSTN Usage sub-tab below. The new PSTN usages can be created under Associated PSTN Usages table in the voice policy form.
 PSTN Usage Home screen
PSTN Usage Home screen
Please create, modify, or delete trunk configurations in Trunk Configuration sub-tab below:
 Trunk Configuration Home screen
Trunk Configuration Home screen
Please create, modify, run, or delete test cases in Test Voice Routing sub-tab below:
 Test Voice Routing Home screen
Test Voice Routing Home screen
Please try the import/export functionality in Voice Routing sub-tabs. You may export your voice- routing configuration to a file. Also, you may import the voice-routing configuration from the file. This functionality is present in every sub-tab under voice routing as shown below:
 Import/Export Configuration
Import/Export Configuration
Similarly, you can import/export voice routing test cases in Voice Routing tabs. Also, you can create test cases. This functionality is also present in all voice routing sub-tab as shown below:
 Import/Export/Create Test Cases
Import/Export/Create Test Cases
Please try creating and running test cases with this functionality as shown below:
 Create Test Cases
Create Test Cases
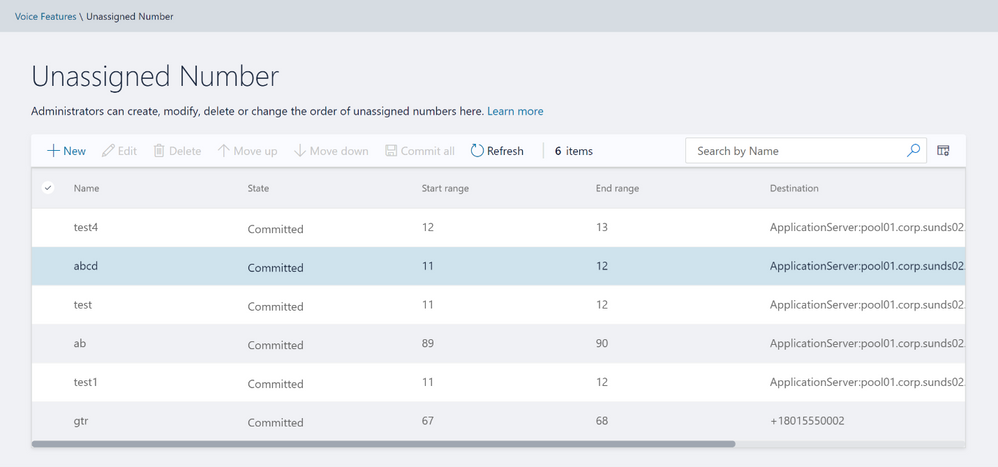
Voice Features
Please try out the scenarios for ‘Call Park’ and ‘Unassigned Number’. You can create various number ranges, edit them, or delete them.
 Call Park home screen
Call Park home screen
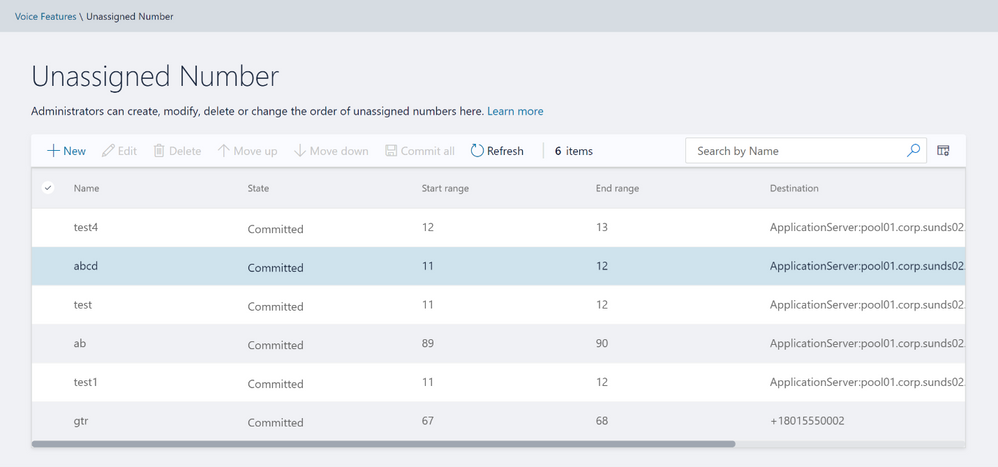 Unassigned Number home screen
Unassigned Number home screen
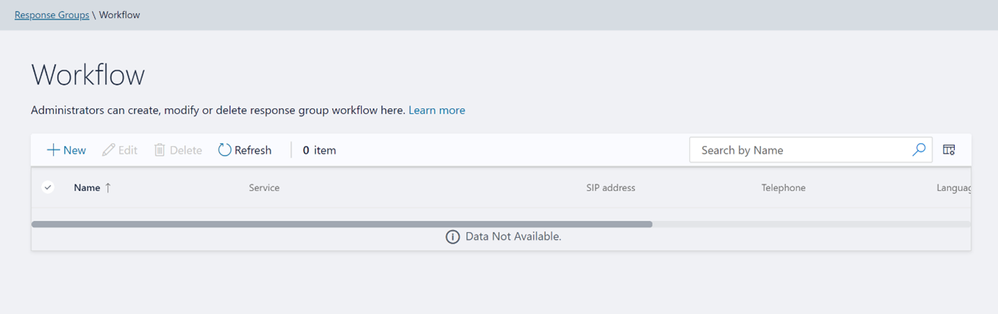
Response Group
Please note that to create or edit a workflow you need to access the page from inside domain network.
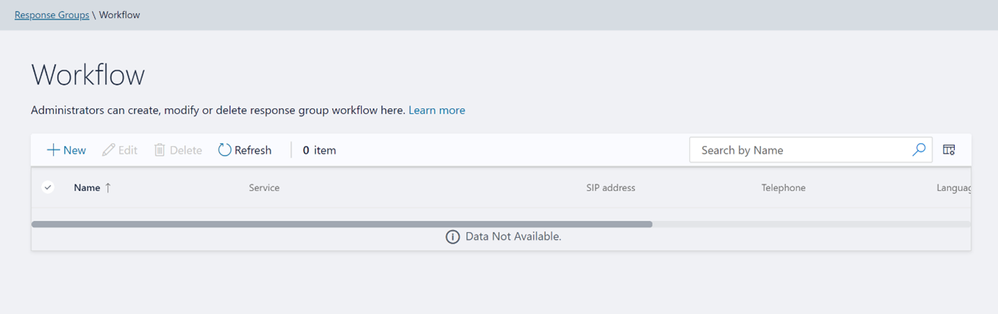 Workflow page in Response Group
Workflow page in Response Group
If not accessing from inside domain network, then the page displays message as shown below:
 Workflow Access from domain message
Workflow Access from domain message
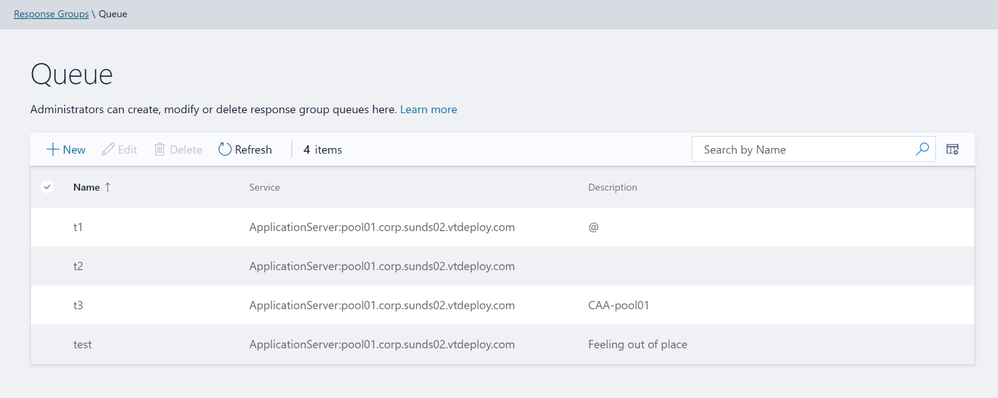
Please create, modify, or delete Response Group Queues in Queue page below:
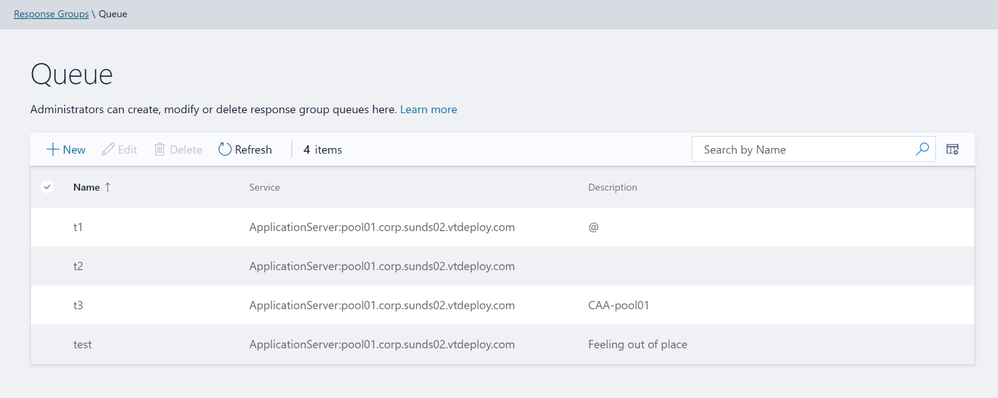 Queue page in Response Groups
Queue page in Response Groups
Please create, modify, or delete group agents in Group page below:
 Group page in Response Groups
Group page in Response Groups
Conferencing
We have also provided the only remaining page from Conferencing tab – ‘Dial-In-Access Number’.
 Dial-In-Access Number in Conferencing
Dial-In-Access Number in Conferencing
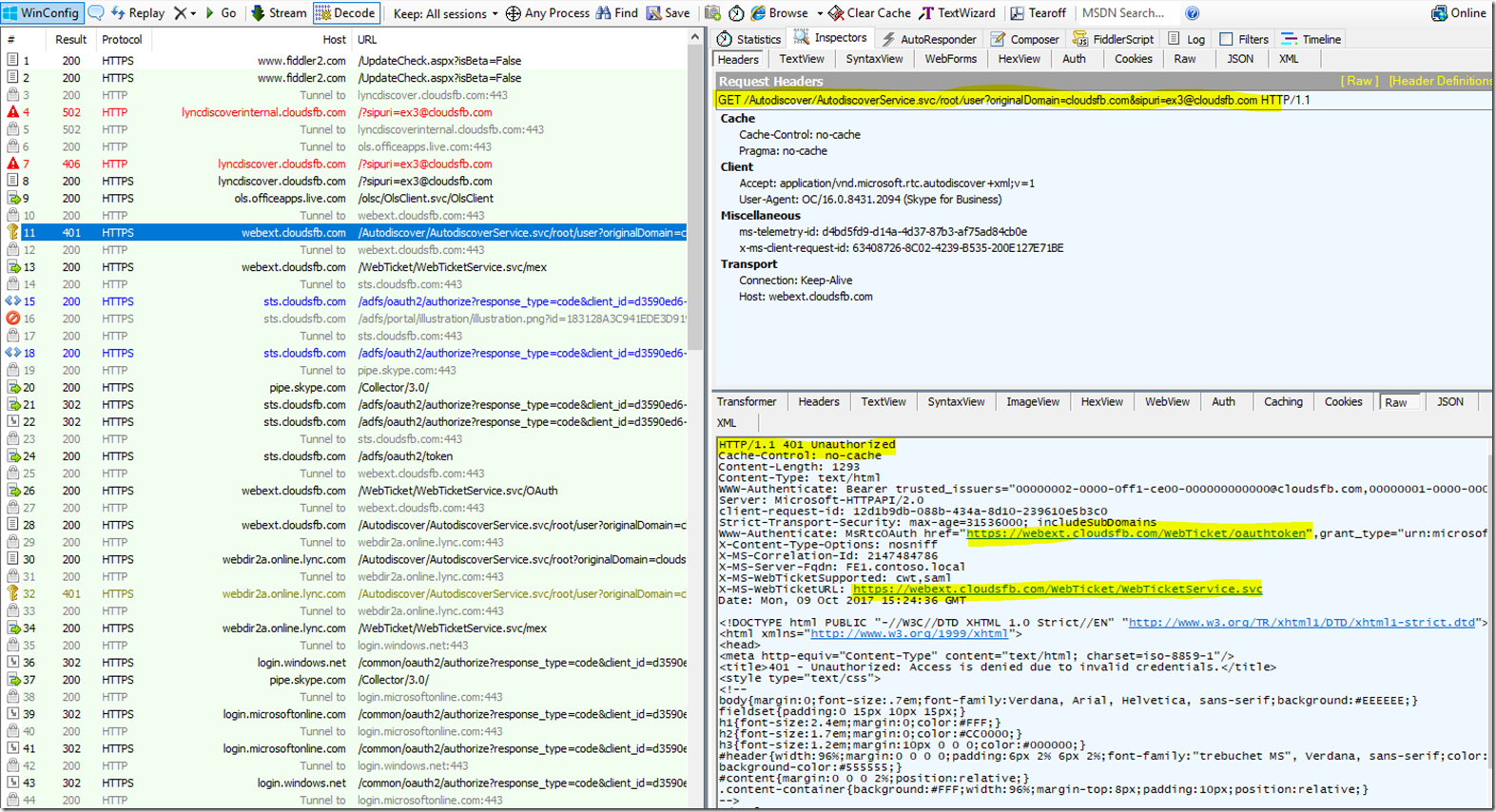
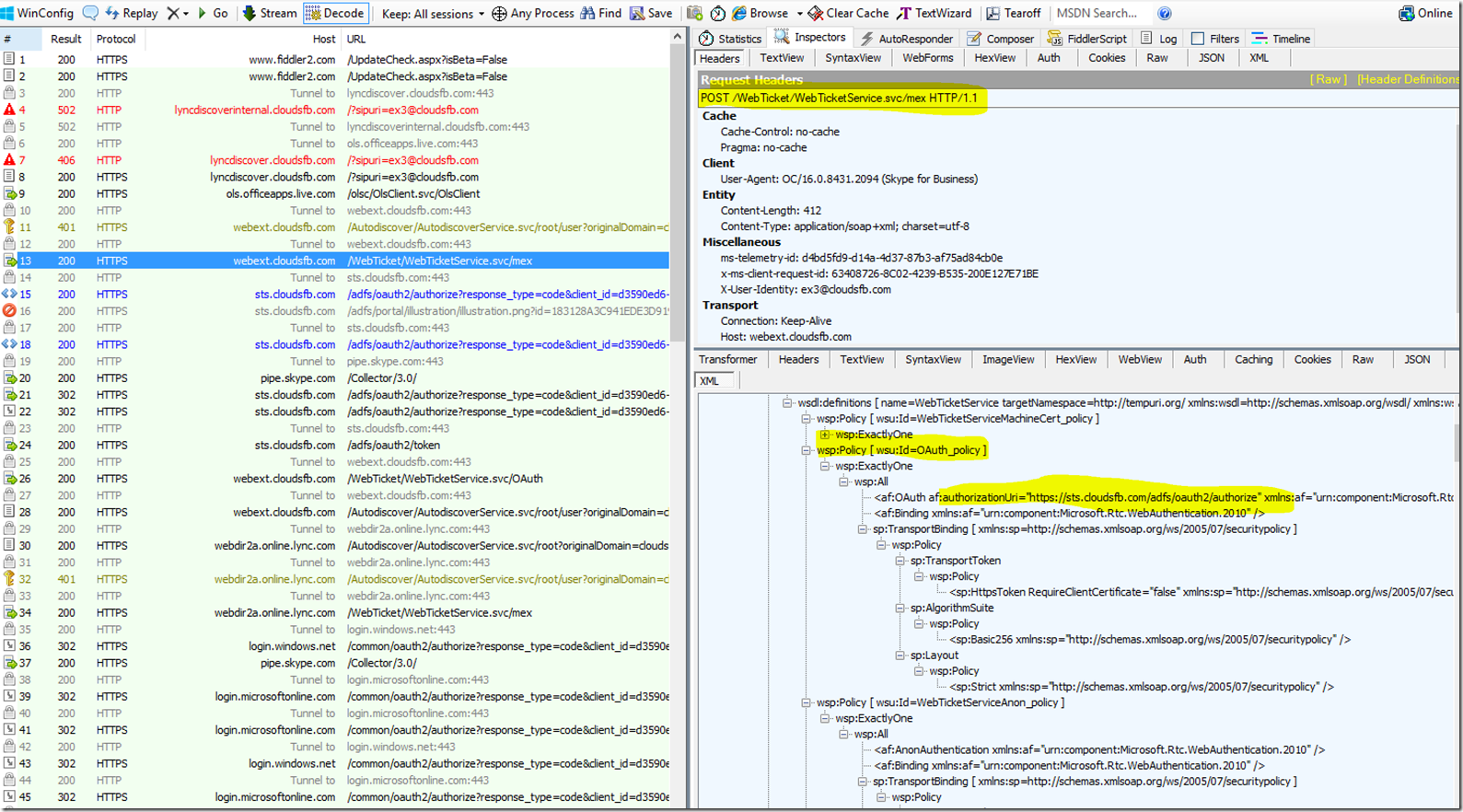
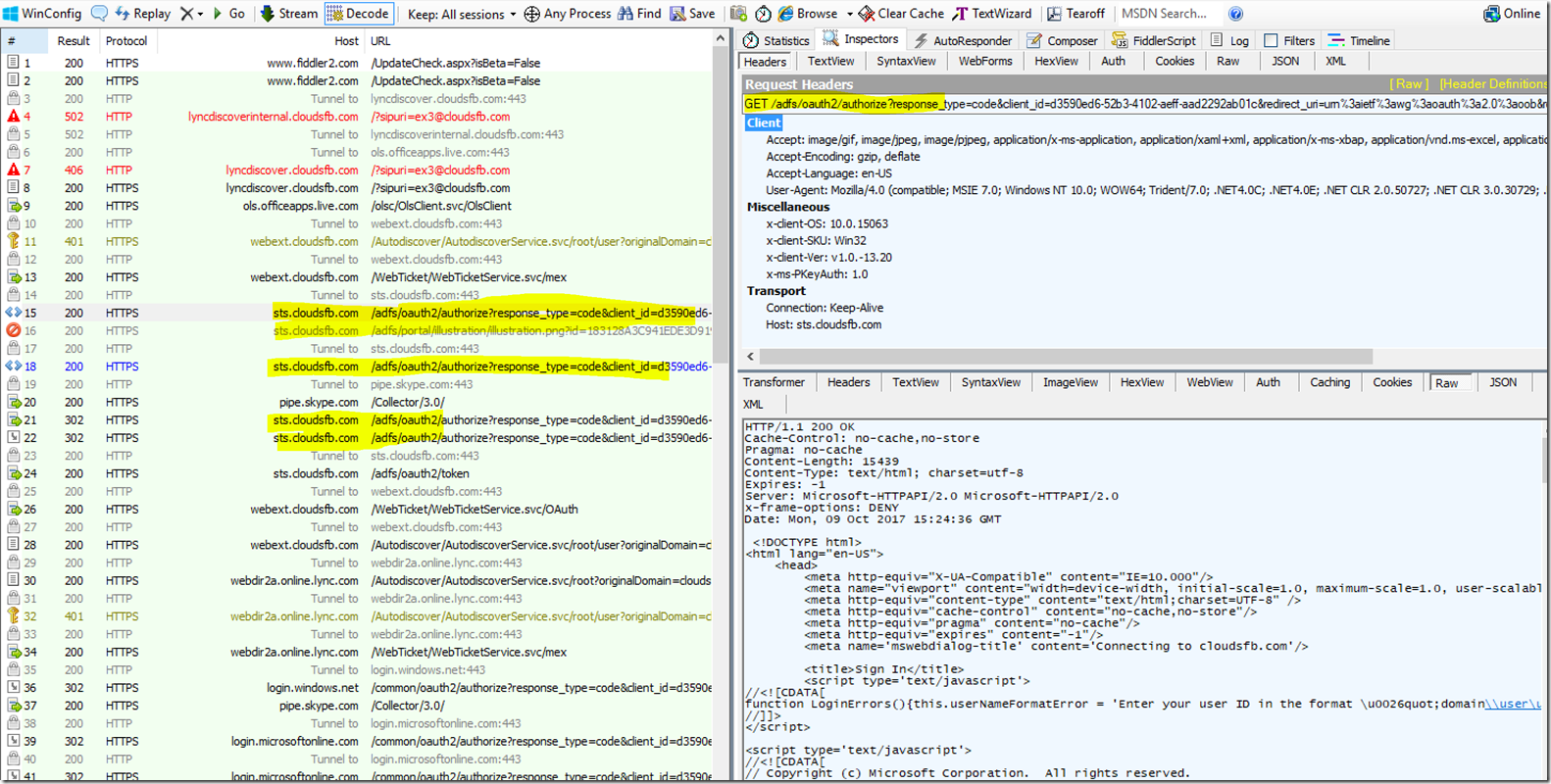
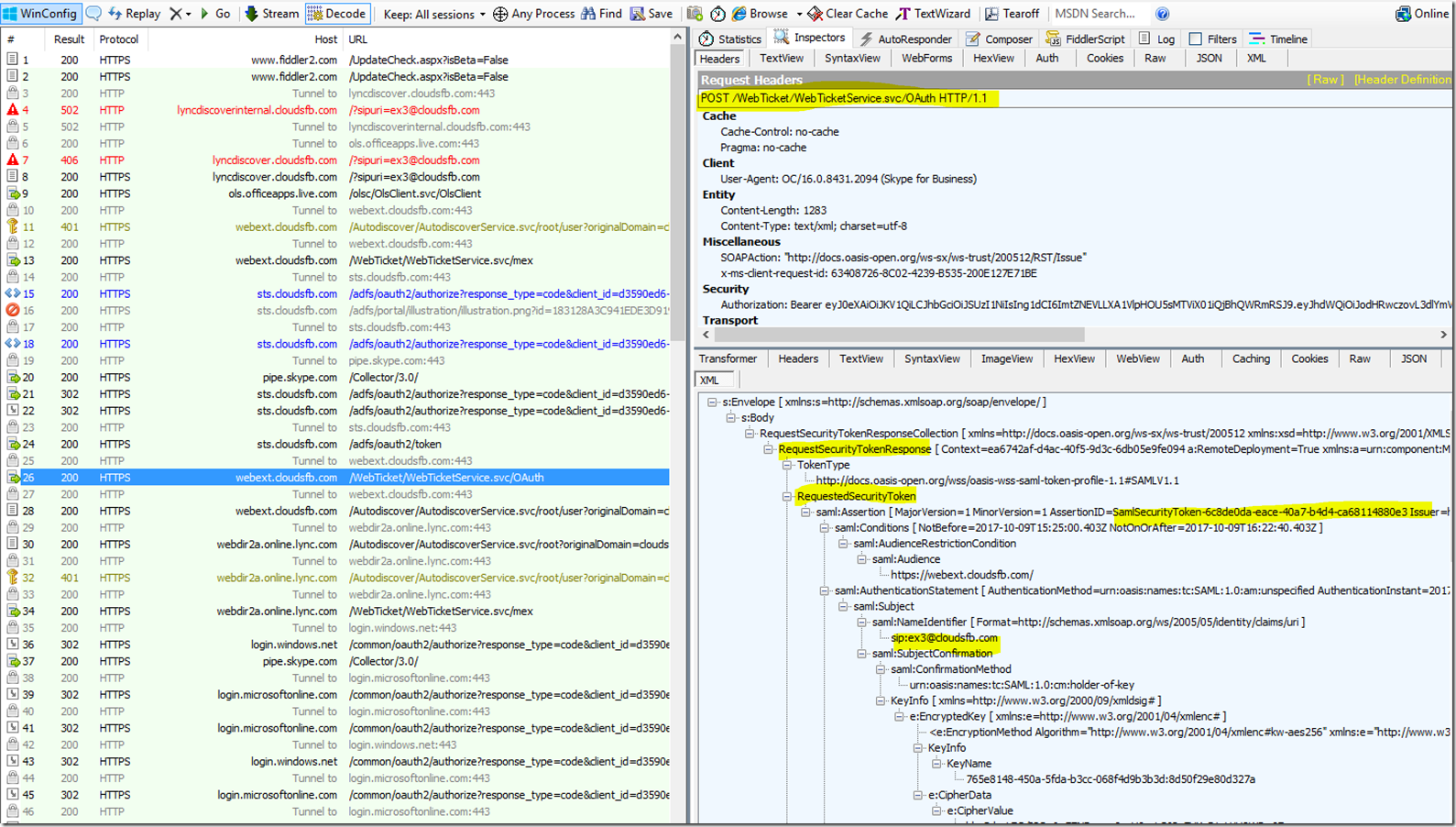
Setup OAuth to login into MACP portal
The following is the step by step process to setup OAuth for MACP portal.
Minimum OS req and ADFS Server version:
- Windows Server 2016 onwards
Steps to be performed on ADFS Farm machine:
- Ensure that an ADFS farm exists on the topology
- Create a new app for MACP in the ADFS
a. Use the script Configure MACP application in ADFS Farm
b. We suggest you go with default options while running the above script.
Steps To be performed on FE w17 server:
Once you have setup the ADFS farm, execute the following steps.
- Install the latest SSUI in all the FE pool machines
- To enable the ADFS OAuth for MACP across all the pools or selective pools
a. Use the script Configure OAuth for MACP
b. We suggest you review default options while running the above script.
NOTE:
- You need to run the script on just one FE W17 server machine in your topology and it will automatically identify all the FEs in your topology (or the selective pools you have passed to the script).
- Use the same script to disable ADFS OAuth and fallback to web-ticket auth.
- To re-configure any ADFS related details, you must disable ADFS OAuth using Configure OAuth for MACP and then configure the ADFS again.
If OAuth is correctly configured, then you should see login screen as below:
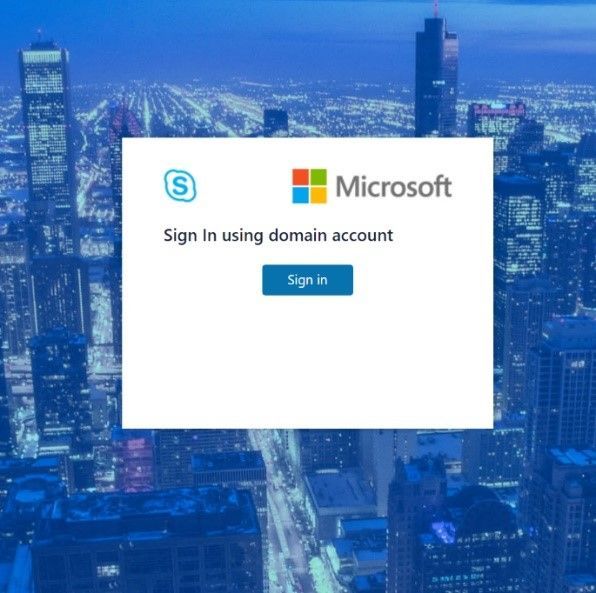
On clicking the Sign in button, you will get a pop-up to enter your username and password.

Setup Simple URL to access the MACP portal
You can also access MACP using the simple URL https://admin.<your-domain>.com
Use the following steps to configure simple URL
1. Install the latest SSUI
2. Configure Simple URL using cmdlet.
Example below shows how a new URL can be added to an existing collection of simple URLs
$urlEntry = New-CsSimpleUrlEntry -Url “https://admin.<your-domain>.com”
$simpleUrl = New-CsSimpleUrl -Component "macp" -Domain "your-domain.com" -SimpleUrlEntry $urlEntry -ActiveUrl “https://admin.<your-domain>.com”
Set-CsSimpleUrlConfiguration -Identity "Global" -SimpleUrl @{Add=$simpleUrl}
3. Run Enable-CsComputer
4. In addition, you must also do such things as
a. create Domain Name System (DNS) records for each URL
b. configure reverse proxy rules for external access
c. add the simple URLs to your Front End Server certificates; and so on.
NOTE:
- Configuring OAuth based authentication for MACP is a prerequisite to use of Simple URL.
Providing Feedback
We always welcomes any feedback and suggestions. Please share feedback and questions via the ‘Give Feedback’ link in the Control Panel. In the top right corner, you’ll see your login name. Click on the adjacent arrow, and you should see a drop-down like the below:

Hit ‘Give Feedback’, and you should see a browser window open with the relevant discussion forum. Please do check the discussions to see if your question has already been addressed. We look forward to hearing from you!
On behalf of the product team,
Ravindra Singh Bisht
Senior Program Manager, Skype for Business Server