Microsoft Azure SRE Agent and Arc enabled Windows Server 2025
Bringing Reliability to the Edge: Azure SRE Agent Meets Windows Server 2025 with Arc for Adaptive Cloud
The next wave of hybrid cloud operations is no longer about simply connecting servers to Azure—it’s about giving every workload, wherever it runs, the same intelligent operational experience as native cloud services. With Windows Server 2025, Azure Arc, and the new Microsoft Azure SRE Agent, Microsoft is closing the gap between cloud and datacenter in a way that finally feels unified.
This post explores how these technologies fit together and why they matter for modern SRE, operations, and hybrid cloud engineering.
Why Azure SRE Agent Changes the Game
Azure SRE Agent is Microsoft’s new operational automation platform designed to reduce toil, accelerate incident response, and build institutional knowledge over time. It’s not just a bot—it’s an AI‑driven operational brain that learns your environment and executes tasks across Azure and hybrid systems.
- It automates operational work so teams can focus on high‑value tasks
- It connects observability tools, incident platforms, and source code systems to automate end‑to‑end workflows
- It continuously builds expertise on your environment and remembers every investigation
- It manages all Azure services through Azure CLI and REST APIs, including compute, storage, networking, databases, and monitoring
What makes SRE Agent unique is its learning loop. Every incident, every triage, every fix becomes part of a persistent knowledge base that never leaves your environment. New engineers ramp faster, and on‑call becomes more consistent and predictable.
Windows Server 2025: Built for Adaptive Cloud
Windows Server 2025 is the most cloud‑aligned release of Windows Server to date. It brings:
- Deep Azure Arc integration
- Modernized SMB, storage, and security
- Hotpatching for non‑Azure VMs
- Enhanced virtualization and container support
- A platform designed for Adaptive Cloud—Microsoft’s strategy to unify cloud and edge operations
But the real magic happens when you connect Windows Server 2025 to Azure Arc and layer the SRE Agent on top.
Azure Arc: The Bridge to Adaptive Cloud
Azure Arc turns any server—physical, virtual, on‑premises, or multi‑cloud—into a first‑class Azure resource. For Windows Server 2025, Arc is not an add‑on; it’s the operational backbone.
With Arc, you get:
- Azure Policy for servers
- Azure Monitor and Log Analytics
- Update management
- Security baselines
- Inventory and change tracking
- GitOps for configuration
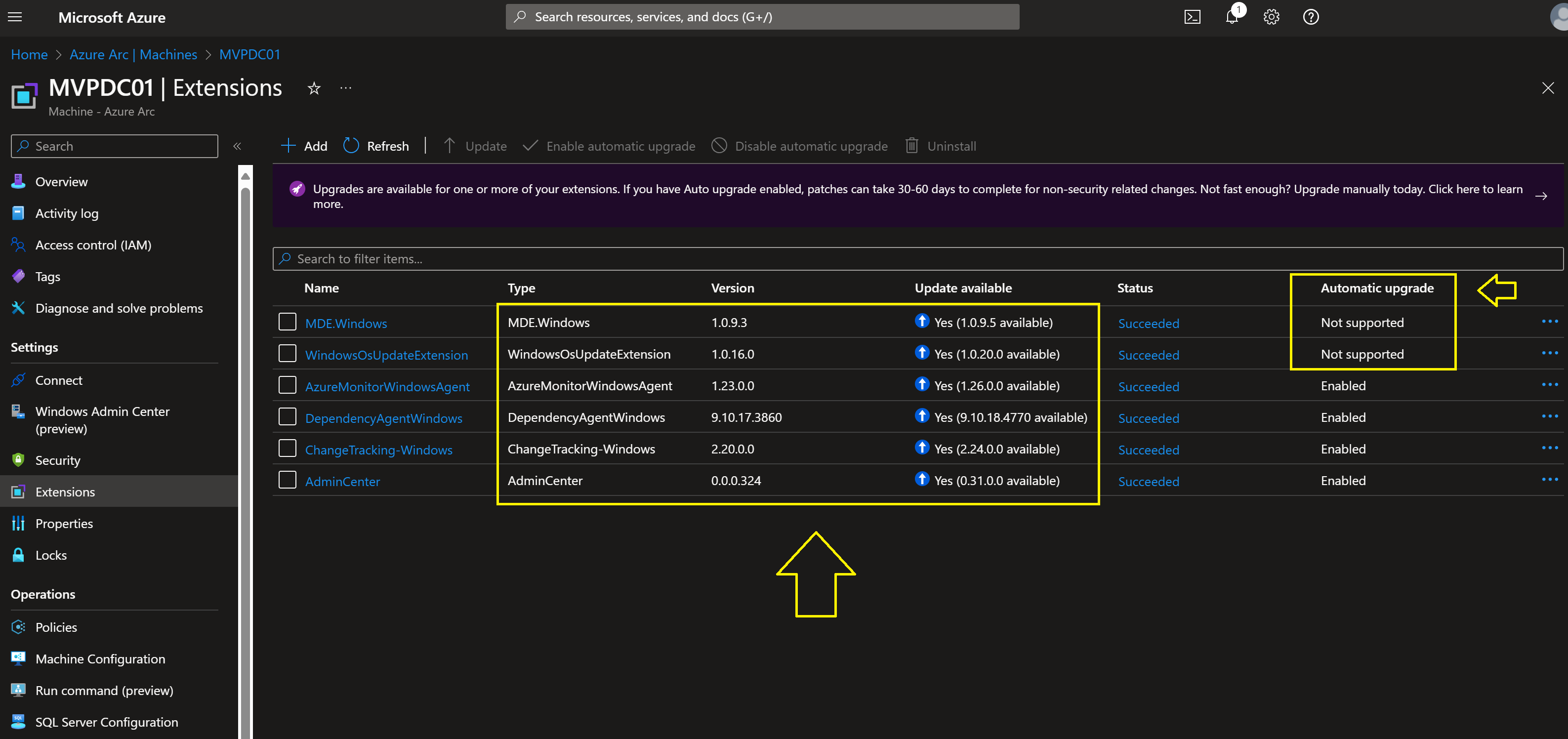
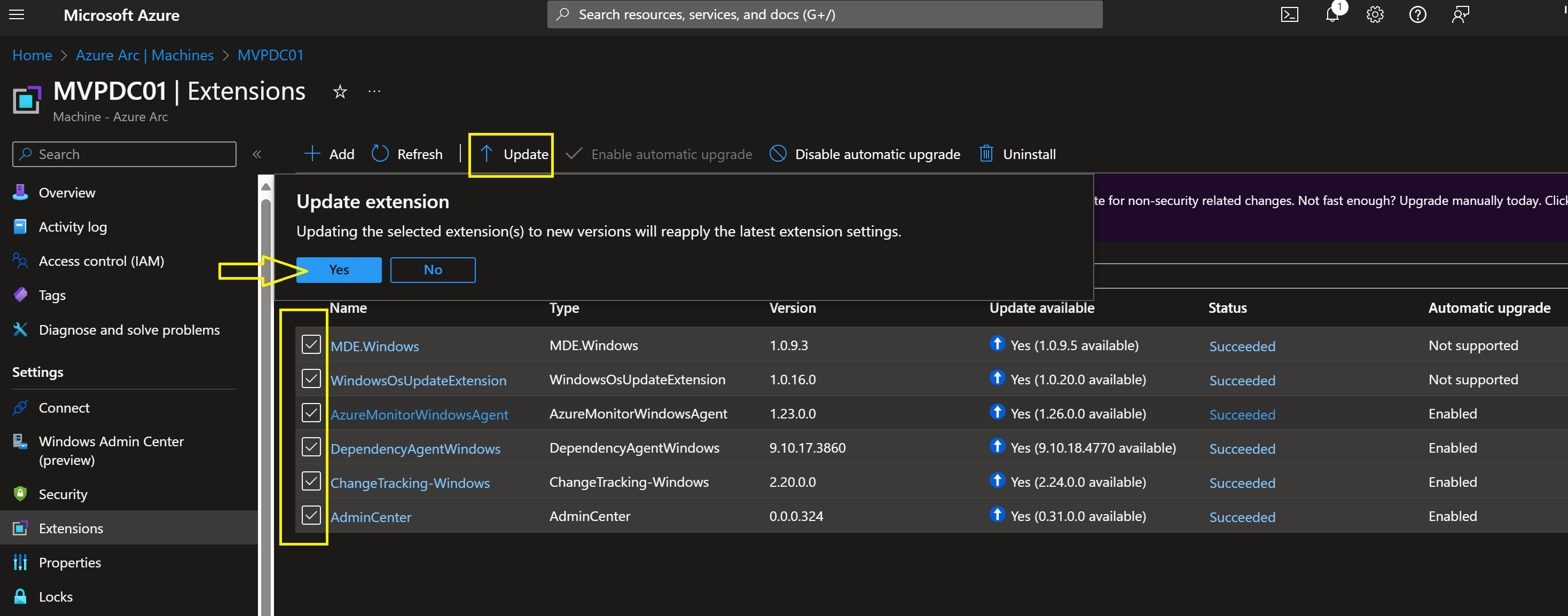
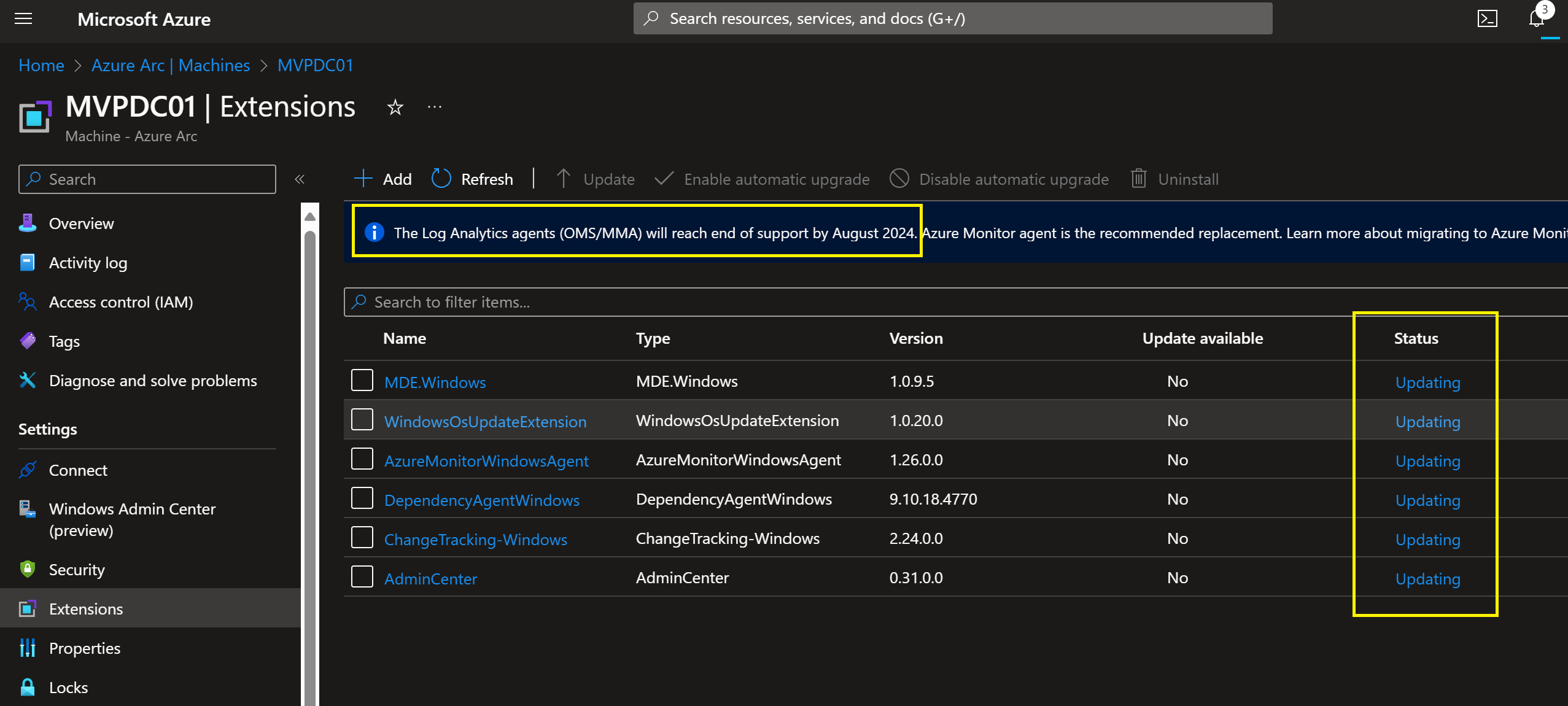
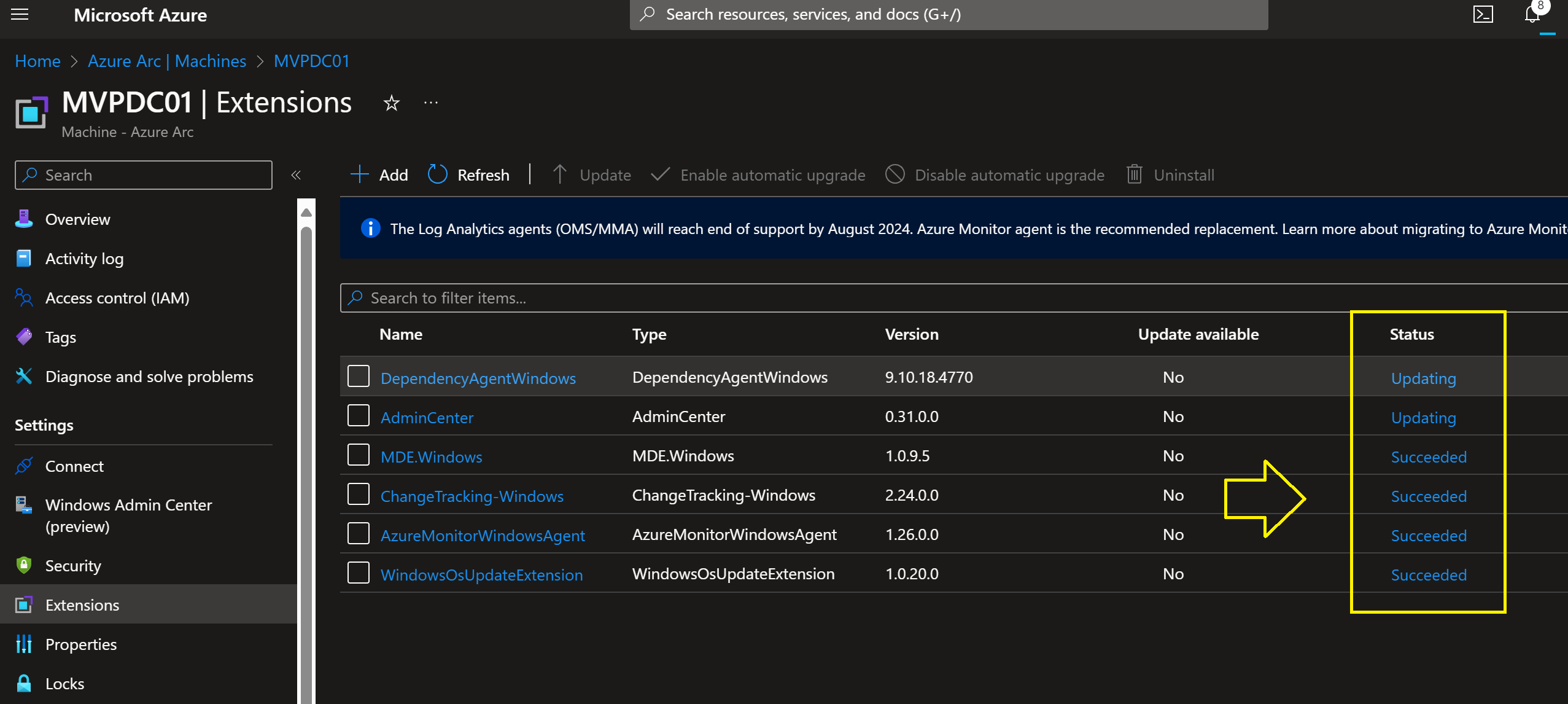
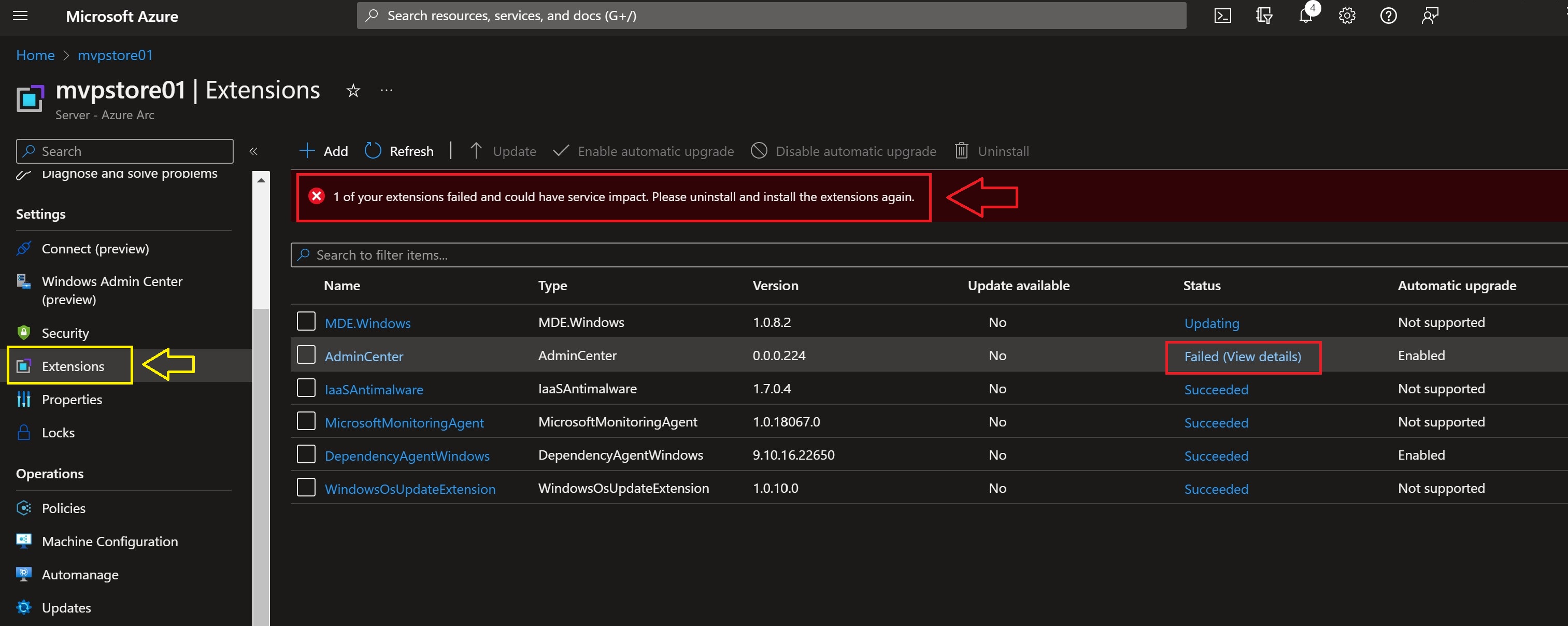
- Arc‑enabled VM extensions (including custom agents)
This is where the SRE Agent fits perfectly.
How Azure SRE Agent Complements Arc‑Enabled Windows Server 2025
- Unified Observability and Incident Automation
Arc brings Windows Server 2025 into Azure Monitor and Log Analytics.
SRE Agent then uses those signals to:
- Automate triage
- Trigger runbooks
- Correlate recurring alerts
- Reduce alert fatigue
- Generate weekly hygiene and monthly threshold audits
Because SRE Agent integrates natively with Azure Monitor alerts, Application Insights, and Log Analytics, it becomes the automation layer on top of Arc’s observability foundation.
- Runbooks and Subagents for Hybrid Operations
SRE Agent supports:
- Custom runbooks
- Azure CLI automation
- REST API calls
- Subagents for specialized services (VMs, databases, networking)
This means you can automate:
- Windows Server 2025 patching
- Storage troubleshooting
- Network diagnostics
- Service restarts
- Log collection
- Configuration drift correction
All triggered by alerts, schedules, or incidents.
- Institutional Knowledge for Hybrid Environments
Every investigation teaches the agent something new:
- Root causes
- Resolution steps
- Team preferences
- Operational patterns
This knowledge persists across conversations and across your hybrid estate.
For organizations with large Windows Server fleets, this is transformative.
- Consistent Operations Across Cloud and Datacenter
Adaptive Cloud is about making on‑prem feel like Azure.
With Arc + SRE Agent:
- Azure Monitor alerts → same experience
- Incident workflows → same experience
- Automation → same experience
- Knowledge base → shared across environments
Windows Server 2025 becomes a true extension of Azure—not just connected, but operationally unified.
A Practical Example: Automated Incident Response on Windows Server 2025
Imagine a Windows Server 2025 VM running on‑prem, Arc‑enabled, and monitored by Azure Monitor.
- Disk latency spikes
Azure Monitor fires an alert. - SRE Agent receives the alert
It correlates with similar incidents from the past month. - Agent runs diagnostics
Using Azure CLI and REST API automation through Arc. - Agent identifies the root cause
A runaway process consuming I/O. - Agent mitigates automatically
- Restarts the service
- Collects logs
- Updates the incident ticket
- Suggests preventive actions based on historical patterns
This is not theoretical—this is exactly what SRE Agent is designed to do.
Why This Matters for SRE and Ops Teams
Less Toil, More Engineering
SRE Agent automates the repetitive work that burns out on‑call engineers.
Faster MTTR
Automated triage and mitigation reduce downtime dramatically.
Better On‑Call Experience
New engineers inherit the agent’s knowledge from day one.
Consistent Hybrid Operations
Arc + SRE Agent gives you a single operational model across cloud and datacenter.
Future‑Proofing
Windows Server 2025 is built for Adaptive Cloud, and SRE Agent is the automation engine that makes it real.
Conclusion: The Future of Hybrid Reliability Engineering
The combination of:
- Windows Server 2025
- Azure Arc
- Azure SRE Agent
creates a hybrid environment where operational excellence is built‑in, not bolted on.
SRE Agent brings intelligence and automation.
Arc brings governance and observability.
Windows Server 2025 brings a modern, cloud‑aligned OS.
Together, they deliver the most complete Adaptive Cloud experience Microsoft has ever offered.
If you’re building a hybrid environment that needs reliability, automation, and consistency, this trio should be at the top of your roadmap.
Important Note: Always test first this configuration in a test environment before you go into production.
Here you find more information about Azure SRE Agent to get Started
Step‑by‑Step: Deploying SRE Agent for Arc‑Enabled Servers
Below is a practical, engineering‑focused workflow you can use in production.
-
Prerequisites
Before deploying SRE Agent, ensure:
 Windows Server 2025 is Arc‑enabled
Windows Server 2025 is Arc‑enabled
Your server must appear as a connected machine in Azure Arc.
 Azure Monitor Agent (AMA) is installed
Azure Monitor Agent (AMA) is installed
SRE Agent relies on metrics, logs, and alerts from Azure Monitor to drive investigations and automations.
 Log Analytics workspace is configured
Log Analytics workspace is configured
This is where SRE Agent queries logs and correlates signals during root cause analysis.
 You have permissions
You have permissions
You need:
- Azure Contributor (or custom role with ARM + extension permissions)
- Ability to deploy VM extensions to Arc machines
-
Create Your SRE Agent in the Portal
- “Create and set up your first agent” is the starting point for onboarding
In Azure Portal:
- Search for Azure SRE Agent
- Select Create Agent (NEW then you go to https://sre.azure.com)

- Sign in with your Azure Account.

- Choose:
- Assign an Agent name
- Select your Model provider ( Important: Learn more about your data protection)
- Link your Log Analytics workspace
This creates the operational brain that will manage your hybrid servers.
-
Connect SRE Agent to Your Arc‑Enabled Servers
SRE Agent works across any Azure resource accessible via ARM, Azure CLI, or REST APIs
For Arc‑enabled servers, this means:
Option A — Use the SRE Agent Portal
Option B — Use Azure CLI
az sre agent resource add \
This registers the server so SRE Agent can query logs, metrics, and run automations.
-
Add Runbooks, Docs, and Custom Logic
You can “enhance your agent with runbooks, architecture docs, and domain‑specific custom agents”
For Windows Server 2025, common runbooks include:
- Restarting Windows services
- Collecting event logs
- Checking disk latency
- Resetting IIS pools
- Running PowerShell remediation scripts
- Triggering Arc extension installs
Upload these into the SRE Agent portal under Automation.
-
Configure Alerts to Trigger SRE Agent
SRE Agent delivers “autonomous incident response” by reacting to Azure Monitor alerts
For Arc‑enabled servers:
- Open Azure Monitor → Alerts
- Create rules for:
- CPU spikes
- Memory pressure
- Disk latency
- Service crashes
- Security events
- Set Action Group → SRE Agent
Now SRE Agent will automatically:
- Gather context
- Query logs, metrics, traces
- Identify root cause
- Suggest or execute mitigations
-
Enable Scheduled Tasks for Routine Operations
SRE Agent can run scheduled tasks for routine operations
For Windows Server 2025, useful schedules include:
- Daily health checks
- Weekly patch compliance scans
- Monthly configuration drift audits
- Log cleanup routines
- Certificate expiry checks
These tasks run across Arc‑enabled servers without needing Azure Automation or DSC.
-
Let the Agent Learn Your Environment
SRE Agent improves over time:
- Day 1: Answers questions, runs queries, analyzes metrics
- Week 1: Learns team patterns and critical metrics
- Month 1: Recognizes recurring issues and applies past learnings automatically
This is especially powerful in hybrid environments where operational knowledge is often tribal and undocumented.
What You Gain After Deployment
Once SRE Agent is fully connected to your Arc‑enabled Windows Server 2025 fleet, you get:
- Autonomous Incident Response
Triggered by Azure Monitor alerts, SRE Agent performs triage, root cause analysis, and remediation.
- Multi‑Signal Correlation
It queries logs, metrics, traces, and deployment history simultaneously to identify issues faster
- Extensible Automation
Built‑in connectors plus MCP integrations for Slack, Jira, Datadog, and internal APIs
- Knowledge That Never Leaves
Every investigation is stored as persistent operational knowledge for your team
- Unified Hybrid Operations
Arc + SRE Agent gives you a consistent operational model across cloud and datacenter.
Conclusion
Deploying Azure SRE Agent on Arc‑enabled Windows Server 2025 is one of the most impactful steps you can take toward a true Adaptive Cloud environment. You get:
- Cloud‑grade automation
- Hybrid observability
- AI‑driven incident response
- Persistent operational knowledge
- A unified experience across your entire estate
This is the future of hybrid SRE — and it’s available today!




 Table of Contents
Table of Contents 1. Compute & VM Sizes
1. Compute & VM Sizes 2. OS Image (Windows Server 2025)
2. OS Image (Windows Server 2025) 3. OS Disk Options
3. OS Disk Options 4. Data Disks
4. Data Disks 5. Networking
5. Networking 6. Public IP Options
6. Public IP Options 7. Boot Diagnostics
7. Boot Diagnostics 8. Managed Identity
8. Managed Identity 9. VM Generation (Gen2)
9. VM Generation (Gen2) 10. Availability Options
10. Availability Options 11. VM Extensions
11. VM Extensions 12. Disk Encryption
12. Disk Encryption 13. Azure AD Login for Windows
13. Azure AD Login for Windows 16. Load Balancer Integration
16. Load Balancer Integration 18. Auto-Shutdown
18. Auto-Shutdown 19. Spot VM
19. Spot VM 20. Azure Hybrid Benefit
20. Azure Hybrid Benefit 21. Dedicated Host
21. Dedicated Host 22. Backup
22. Backup 24. Azure Compute Gallery
24. Azure Compute Gallery 25. VM Scale Sets (VMSS)
25. VM Scale Sets (VMSS) 26. WinRM Configuration
26. WinRM Configuration 27. Guest Configuration Policies
27. Guest Configuration Policies Final Thoughts
Final Thoughts
 Are all the JSON examples fully functional and tested in Azure?
Are all the JSON examples fully functional and tested in Azure? Fully functional & deployable as‑is
Fully functional & deployable as‑is Fully valid, but require environment‑specific resources
Fully valid, but require environment‑specific resources Requires a Disk Encryption Set + Key Vault.
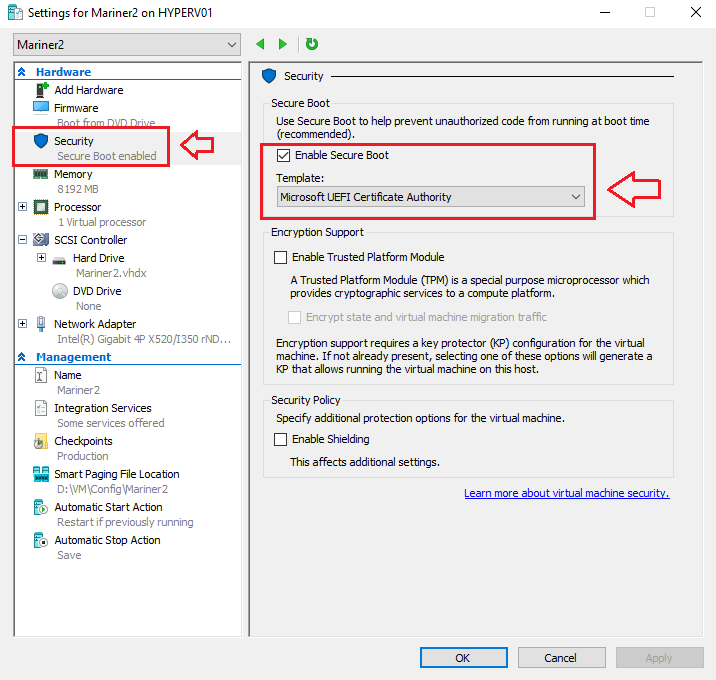
Requires a Disk Encryption Set + Key Vault. Trusted Launch & Confidential Computing
Trusted Launch & Confidential Computing