Planning the Transition: Upgrading from Windows 10 to Windows 11 in Enterprise Environments
Windows 10 Laptop needs Upgrade 
Planning the Transition: Upgrading from Windows 10 to Windows 11 in Enterprise Environments
The upgrade from Windows 10 to Windows 11 offers enterprise businesses exciting opportunities to enhance productivity, security, and the overall user experience. However, this transition requires thoughtful planning, especially when deploying at scale across varied environments. Let’s explore how enterprises can prepare for a seamless upgrade, considering scenarios like using Microsoft Intune, MECM, or focusing solely on the end-user perspective.
 IMPORTANT: Windows 10 will be supported until October 14, 2025. After this date, Microsoft will no longer provide technical support or security updates for Windows 10. (You can join ESU Program for Windows 10 if necessary)
IMPORTANT: Windows 10 will be supported until October 14, 2025. After this date, Microsoft will no longer provide technical support or security updates for Windows 10. (You can join ESU Program for Windows 10 if necessary)
Understanding the Upgrade Landscape
Before diving into deployment strategies, enterprises should consider:
- System Requirements: Ensure devices meet Windows 11 hardware requirements. Tools like the PC Health Check app can help.
- Application Compatibility: Use Microsoft’s App Assure to verify that critical business applications work smoothly.
- Infrastructure Readiness: Decide whether your deployment will be managed through on-premises infrastructure, cloud-based management, or a hybrid approach.
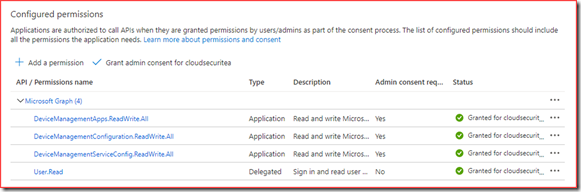
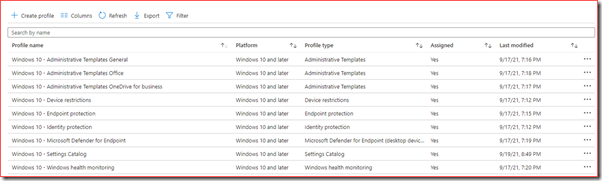
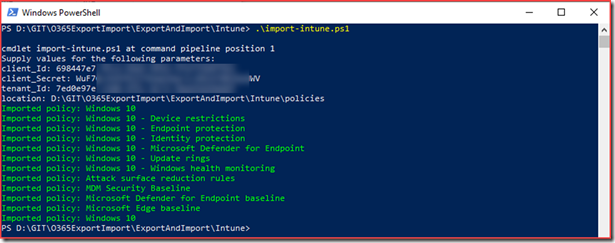
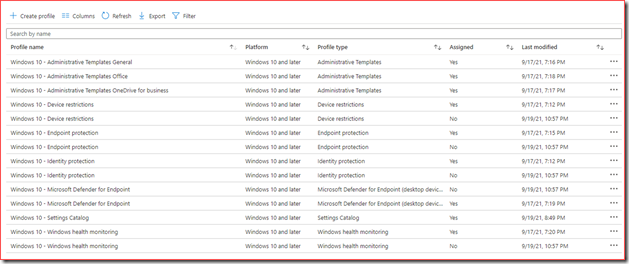
Scenario 1: Deployment Using Microsoft Intune
Microsoft Intune is an excellent choice for organizations embracing a modern, cloud-first management approach. It simplifies remote deployment and is particularly well-suited for enterprises with hybrid or remote workforces.
Steps to Deploy with Intune:
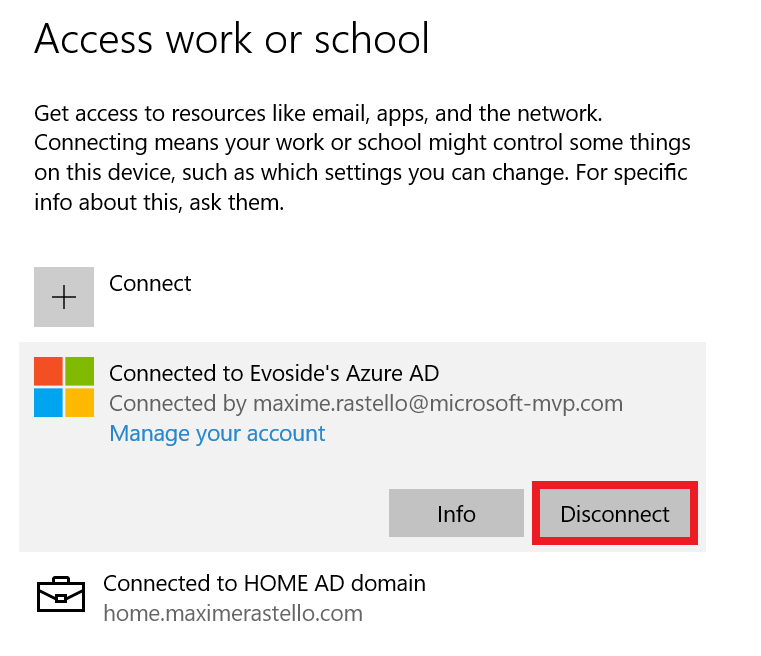
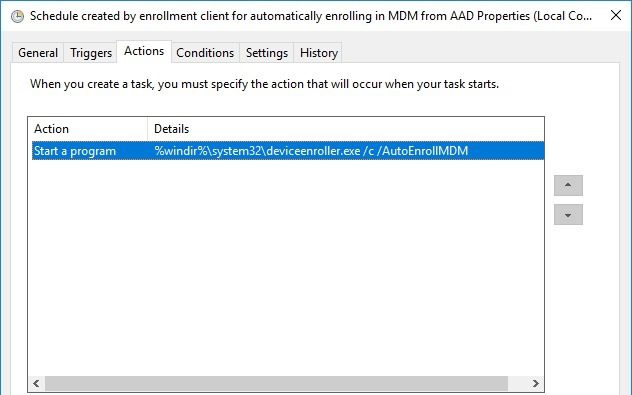
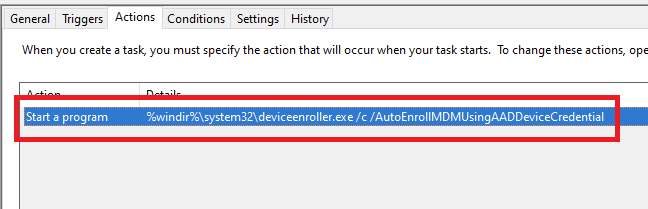
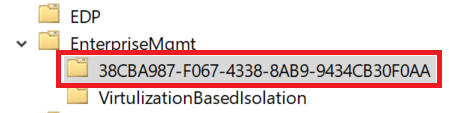
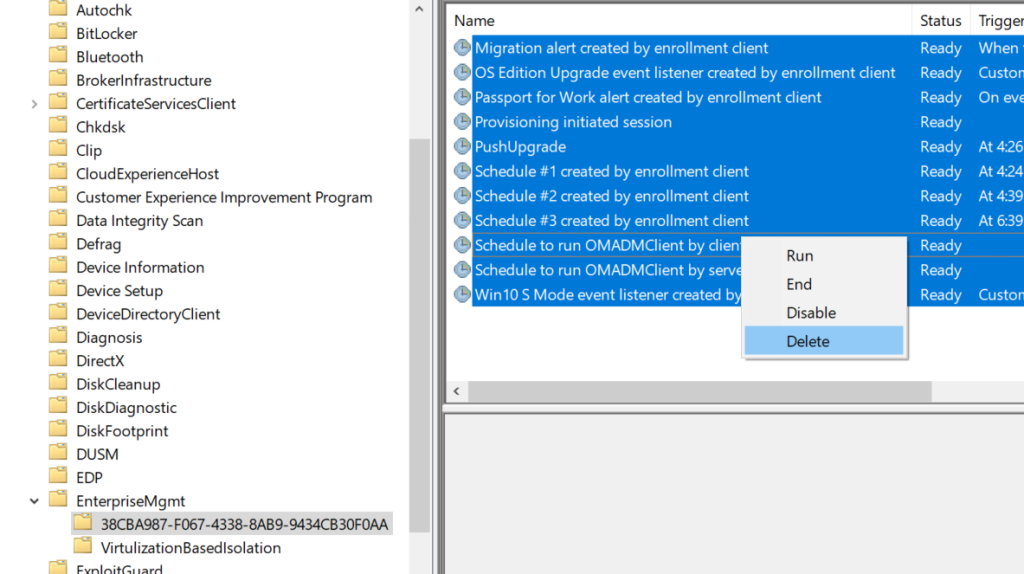
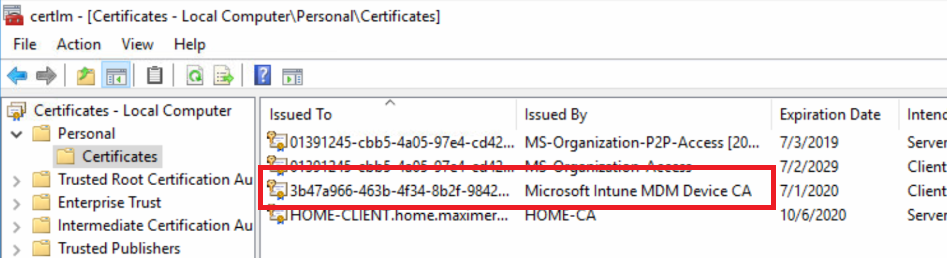
- Prepare Devices: Ensure all devices are enrolled in Intune and compliant with Azure AD.
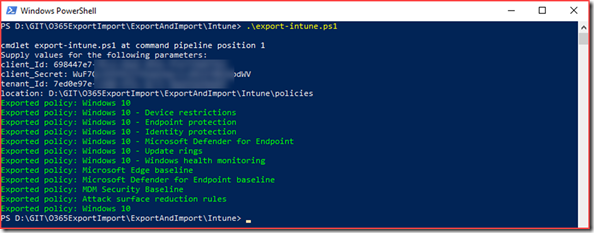
- Set Up Deployment Policies: Use Intune to create a feature update deployment policy that targets eligible devices.
- End-User Impact: Notify employees about the upgrade. With Intune, upgrades are minimally disruptive, allowing installations to occur outside work hours.
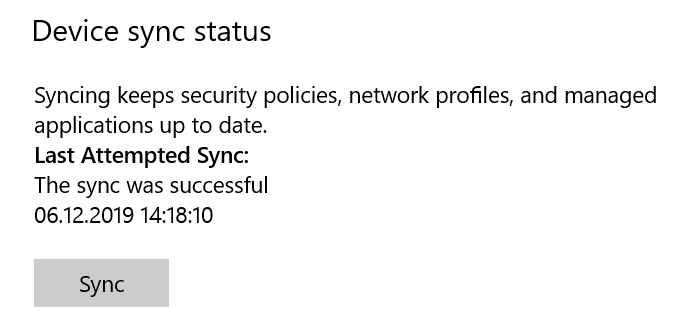
- Monitoring Progress: Use the Intune admin center to track the deployment and address any failed upgrades.
Best Use Case: Organizations prioritizing remote or hybrid work scenarios, or those aiming to reduce reliance on on-premises infrastructure.
Scenario 2: Deployment Using MECM (Microsoft Endpoint Configuration Manager)
MECM provides robust control for enterprises with significant on-premises infrastructure. It’s ideal for managing complex upgrade scenarios, like retaining user profiles and configurations during deployment.
Steps to Deploy with MECM:
- Assess Readiness: Use MECM to run hardware inventory reports and verify device eligibility.
- Prepare the Upgrade Package: Download Windows 11 media and create a task sequence in MECM for an in-place upgrade.
- Deployment Strategy: Schedule phased rollouts, starting with a pilot group before scaling across the organization.
- Monitoring Progress: Leverage MECM’s detailed reporting tools to ensure smooth execution and troubleshoot issues.
Best Use Case: Enterprises requiring greater control over deployment tasks or operating primarily within an on-premises environment.
Scenario 3: Focusing on the End-User Experience
For some organizations, the primary focus of the upgrade is minimizing disruptions for end users and ensuring a seamless experience during and after the transition.
Key Considerations for End Users:
- Communication: Inform employees about what to expect, including changes in interface and new features in Windows 11.
- Training & Support: Offer training sessions or documentation to familiarize users with Windows 11’s productivity enhancements, Microsoft Learn is a great Learning platform for Windows 11 Training
- Feedback Mechanism: Provide a channel for users to report issues or seek support during the rollout.
Best Use Case: Any enterprise prioritizing user satisfaction and productivity during the upgrade.
Recommendations for a Smooth Transition
- Pilot Testing: Start with a small group of users to test the upgrade process and gather insights.
- Backup Strategy: Ensure critical data is backed up before proceeding with mass deployments.
- Define Success Metrics: Monitor upgrade success rates, user satisfaction, and system performance post-upgrade.
Whether you’re leveraging Intune, MECM, or focusing on empowering end users, careful planning and clear communication are the keys to success. With the right approach, your organization can unlock the full potential of Windows 11 while keeping disruptions to a minimum.
Ready to take the first step? Let the upgrade journey begin! 
Here you find more information from Microsoft about Planning for Windows 11
Here you find Microsoft Intune Documentation
Here you find Microsoft Endpoint Configuration Managers Documentation (MECM)
Have a look at Microsoft Copilot + PC to be ready for AI in your Business